Virus library
An analysis of the technologies used by cybercriminals allows us to draw conclusions about the virus industry’s possible vectors of development and more effectively confront future threats. You, too, can learn what actions various malicious programs take in infected systems and how to withstand them.
Linux.Mirai in virus library:
A family of Linux Trojans. One of its representatives is described below.
SHA1:
- 7e0e07d19b9c57149e72a7ed266e0c8aa5019a6f
A modified version of Linux.DDoS.87 and Linux.DDoS.89. Its main differences from Linux.DDoS.89 are as follows:
- Some samples of the Trojan can now delete themselves.
- The Trojan can disable the watchdog timer, which prevents system hangs, to make it impossible to reboot the computer.
- The process’s name is changed to a random sequence containing the characters [a-z 0-9].
- The configuration structure has been changed.
- If a process named “.anime” is found, the Runkiller function not only terminates this process but also deletes the executable file.
- Unlike Linux.DDoS.89, this version can execute HTTP Flood attacks.
- If the Trojan fails to create a socket and connect to it, the corresponding function searches for the process that owns the socket and kills it.
The Trojan’s configuration looks as follows:
| Number | Value | Purpose |
|---|---|---|
| 3 | listening tun0 | main output to stdin |
| 4 | Host | Command and control (C&C) server’s IP address |
| 5 | Port | C&C server’s port |
| 6 | "https://youtube.com/watch?v=dQw4w9WgXcQ" | |
| 7 | "/proc/" | runkiller |
| 8 | "/exe" | runkiller |
| 9 | " (deleted)" | |
| 10 | "/fd" | runkiller |
| 11 | ".anime" | runkiller |
| 12 | "REPORT %s:%s" | runkiller |
| 13 | "HTTPFLOOD" | runkiller |
| 14 | "LOLNOGTFO" | runkiller |
| 15 | "\x58\x4D\x4E\x4E\x43\x50\x46\x22" | runkiller |
| 16 | "zollard" | runkiller |
| 17 | "GETLOCALIP" | |
| 18 | Host | |
| 19 | Port | |
| 20 | "shell" | |
| 21 | "enable" | |
| 22 | "system" | |
| 23 | "sh" | |
| 24 | "/bin/busybox MIRAI" | |
| 25 | "MIRAI: applet not found" | |
| 26 | "ncorrect" | |
| 27 | "/bin/busybox ps" | |
| 28 | "/bin/busybox kill -9 " | |
| 29 | "TSource Engine Query" | |
| 30 | "/etc/resolv.conf" | |
| 31 | "nameserver" | |
| 32 | "Connection: keep-alive" | |
| 33 | "Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8" | |
| 34 | "Accept-Language: en-US,en;q=0.8" | |
| 35 | "Content-Type: application/x-www-form-urlencoded" | |
| 36 | "setCookie('" | |
| 37 | "refresh:" | |
| 38 | "location:" | |
| 39 | "set-cookie:" | |
| 40 | "content-length:" | |
| 41 | "transfer-encoding:" | |
| 42 | "chunked" | |
| 43 | "keep-alive" | |
| 44 | "connection:" | |
| 45 | "server: dosarrest" | |
| 46 | "server: cloudflare-nginx" | |
| 47 | "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/51.0.2704.103 Safari/537.36" | User Agent |
| 48 | "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/52.0.2743.116 Safari/537.36" | User Agent |
| 49 | "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/51.0.2704.103 Safari/537.36" | User Agent |
| 50 | "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/52.0.2743.116 Safari/537.36" | User Agent |
| 51 | "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_11_6) AppleWebKit/601.7.7 (KHTML, like Gecko) Version/9.1.2 Safari/601.7.7" | User Agent |
All samples of the Trojan use a function that hides the following strings:
def decode(str_enc):
return "".join([chr(ord(x) ^ 0x22) for x in str_enc])
Once launched, the Trojan removes its executable file from the disk, blocks the SIGINT signal with the help of sigprocmask, and sets the parameter SIG_IGN for SIGCHLD and a handler for SIGTRAP.
Then the Trojan tries to open the /dev/watchdog file for reading/writing (/dev/misc/watchdog is also checked) and, if successful, disables the watchdog timer.
ioctl(fd, WDIOC_SETOPTION, WDIOS_DISABLECARD)
The Trojan subsequently opens a root folder and sends a request to the address 8.8.8.8:53 to get the IP address of its network traffic.
Next, the Trojan calculates a function taken from the argv[0] value:
def check(name):
print name
a = [ord(x) for x in name]
sum = (0 - 0x51) & 0xff
for i in [2,4,6,8,10,12]:
z = (~a[i % len(a)] & 0xff)
sum = (sum + z)&0xff
#print "%x %x %x" % (z, sum, sum % 9)
return sum % 9This function returns a number from 0 to 8 that represents an index in a function array:
off_8055DC0 dd offset bind_socket ; DATA XREF: main+109o
.rodata:08055DC4 dd offset sub_80517E0
.rodata:08055DC8 dd offset sub_8051730
.rodata:08055DCC dd offset create_config
.rodata:08055DD0 dd offset sub_8051760
.rodata:08055DD4 dd offset sub_80523F0
.rodata:08055DD8 dd offset strcopy
.rodata:08055DDC dd offset runkiller
.rodata:08055DE0 dd offset sub_804E900
If argv[0] == “./dvrHelper”, a parental process receives the SIGTRAP signal (for which a handler was previously installed). The handler, in turn, modifies the IP address taken from the configuration and the C&C server’s port to which the Trojan will connect.
Then a listening socket is opened at the address 127.0.0.1:48101. If this port is busy with another process, the Trojan runs a function that finds the process and kills it.
The Trojan subsequently generates a name that looks like a random sequence containing the characters [a-z 0-9] and writes it to argv[0]. Using the prctl function, the process’s name is changed to a random one.
Next, the Trojan creates child processes and terminates the parental one. All further steps are performed in a child process—in particular, a structure containing handlers is filled in. Then a function responsible for scanning telnet nodes and a function that terminates the processes of other Trojans are launched. The Trojan then runs a handler for incoming instructions sent from the C&C server. If the Trojan detects that a connection to a local server is being established, it runs a child process to scan vulnerable telnet nodes and terminates the parental process.
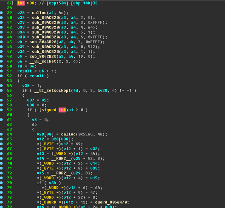
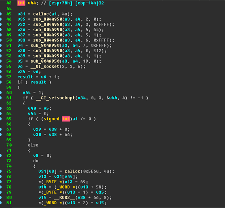
The picture below shows a code fragment for Linux.DDoS.87 (left column) and Linux.Mirai (right column).
Linux.Mirai in virus library:
Linux.Mirai.1080
Linux.Mirai.1121
Linux.Mirai.1122
Linux.Mirai.1123
Linux.Mirai.1124
Linux.Mirai.1169
Linux.Mirai.1194
Linux.Mirai.1195
Linux.Mirai.1196
Linux.Mirai.1197
Linux.Mirai.1198
Linux.Mirai.1220
Linux.Mirai.1233
Linux.Mirai.1235
Linux.Mirai.1245
Linux.Mirai.1277
Linux.Mirai.1397
Linux.Mirai.1398
Linux.Mirai.1399
Linux.Mirai.1450
Linux.Mirai.1465
Linux.Mirai.1491
Linux.Mirai.1509
Linux.Mirai.1514
Linux.Mirai.1530
Linux.Mirai.1538
Linux.Mirai.1545
Linux.Mirai.1548
Linux.Mirai.1549
Linux.Mirai.1596
Linux.Mirai.1597
Linux.Mirai.1598
Linux.Mirai.1600
Linux.Mirai.1601
Linux.Mirai.1625
Linux.Mirai.1628
Linux.Mirai.1635
Linux.Mirai.1639
Linux.Mirai.1653
Linux.Mirai.1654
Linux.Mirai.1855
Linux.Mirai.1893
Linux.Mirai.1915
Linux.Mirai.1968
Linux.Mirai.2011
Linux.Mirai.2012
Linux.Mirai.2135
Linux.Mirai.2136
Linux.Mirai.2137
Linux.Mirai.2138
Vulnerabilities for Android
According to statistics, every fifth program for Android contains a vulnerability (or, in other words, a "loophole") that lets cybercriminals successfully introduce Trojans onto mobile devices and manipulate them into doing whatever actions they need them to.
Dr.Web Security Auditor for Android diagnoses and analyses a mobile device’s security and offers solutions to address security problems and vulnerabilities.