SHA1:
- f9d8a20c5be86876e493ebf80b3d021951a7e344
A Trojan for Android implemented as an advertising SDK (Software Development Kit) platform. It is incorporated into software that can be distributed via various app stores including Google Play.
Once such-like program is launched, Android.Spy.305.origin connects to the http://client.api-*******.com server and sends the following request:
http://client.api-*******.com/v3/upd?app_id=com.mobilescreen.recorder&device_id=86804202*******&access_token=MSDK-10-ok8FmzAh
CJKf4Bo5VVHkqmWWPGShOWIUb1RPNo9t0cgrFDQx77sTGXgjhffEo&publisher=101324582&version=0&android_id=266af8c9e01d0ce
The server replies with URL needed to download an additional component (Android.Spy.306.origin) which is responsible for the Trojan’s main malicious activity that Android.Spy.305.origin performs using the DexClassLoader class.
Then the Trojan sends the following data to the command and control server:
- Email address connected to Google user account
- List of installed applications
- Current system language
- By the device’s manufacturer
- Mobile device model
- IMEI identifier
- OS version
- Screen resolution
- Mobile network operator
- Name of the application containing the Trojan
- Developer’s ID
- SDK platform’s version
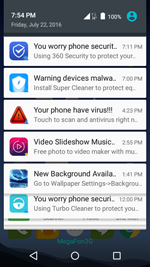
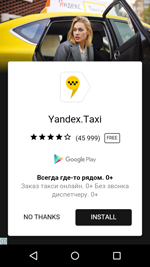
Android.Spy.305.origin can display advertisements on top of running applications and the operation system’s interface. It can also shows ads in the status bar.