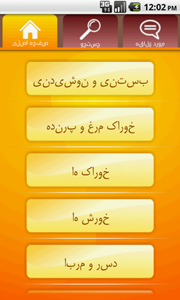
A Trojan for Android mobile devices. The malware is incorporated into a program called Iranian Foods that contains a collection of Iranian cuisine recipes. It can be distributed through various websites that host software and via Internet forums.
 |
 |
Malicious module launches as a stamper service. The service is periodically activated searching for JPEG files in the /DCIM/Camera/ folder where all pictures taken with the camera are stored by default. If any graphics files are found in that location, the Trojan puts an image of Ayatollah Khomeini on every picture.
Pictures modified by the Trojan cannot be restored back to their original state. Moreover, such malicious actions can considerably reduce free memory space, because Android.Moghava can change already modified pictures. The only way to restore modified pictures is to replace them with original copies.

