A malicious program designed to infect ATMs of one international manufacturer. It is distributed in Latin America and is supposedly installed on the system from a bootable CD.
It consists of the following components:
- NCRWMI.exe—an executable file written in Delphi and installed on the system as the NCRDRVP system service. It downloads the SystemP.dll library.
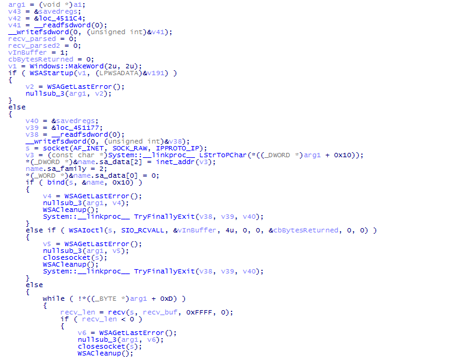
- SystemP.dll—a library written in Delphi. Operating as a sniffer, this library analyzes the whole bulk of IP traffic looking for incoming commands.
The library supports the execution of the following commands:
- 5449610000583686=xxxxxxxxxxxxxxxx—run the Trojan’s executable file with the xxxxxxxxxxxxxxxx parameter (C:\WINDOWS\system32\cmd.exe /c PLOUTOS.EXE 5449610000583686=xxxxxxxxxxxxxxxx).
- 6037428100036810—kill the Ploutos.exe process (C:\WINDOWS\system32\cmd.exe /C START TASKKILL /F /IM Ploutos.exe).
The 5449610000583686=xxxxxxxxxxxxxxxx command can be written on the magnetic strip of a card in the Track 2 section.
- Ploutos.exe—a Trojan’s executable file that controls the infected ATM. It saves its configuration data in the config.ini file to the current folder. The log is saved to the Log.txt file. To perform some of its functions, the Trojan utilizes the ActiveXFSControls.dll dynamic library from the ATM’s SDK.
Parameters the Trojan receives look as follows:
5449610000583686=0123456789abcdYZ, where YZ—command, 0123456789abcd—parameters.
The main module can execute the following commands:
- 5449610000583686=2836957412536985—generate the ID (4 random numbers) and enter the value into the DATAA parameter of the configuration file.
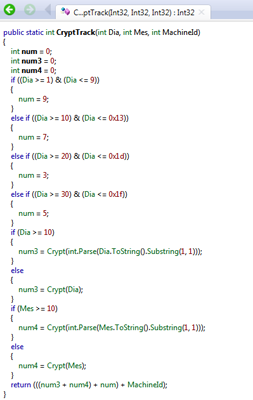
- 5449610000583686=0123456789abcd54—activate the Trojan for 24 hours. The key is calculated using the following method: The operation time is added to the DATAB parameter of the configuration file. The activation key’s md5 value is entered into the DATAC parameter. The3d1905b7 value is taken from the command line as the key.
- 5449610000583686=0123456789abcd31—command to withdraw cash (the number of 40 is hard coded in the Trojan’s body).
This command is executed if a correct ID is specified via the command line (the a28c value is used).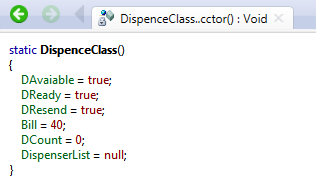
- 5449610000583686=0123456789abcd32—command to terminate the Trojan’s process. It is executed if a correct ID is specified via the command line (the a28c value is used).
- 5449610000583686=0123456789abcd99—command to kill the Trojan’s process (cmd.exe /C TASKKILL /F /IM Ploutos.exe).
The ATM is controlled using XFSVendorModeServiceClass from the ActiveXFSControls.dll library, which is included in the device’s software.
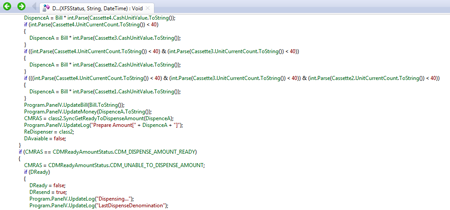
The cash withdrawal routine is implemented as follows: