A malicious program infecting Android handhelds. Can be distributed in the guise of popular applications. A vandal program that wipes removable memory cards and blocks access to certain applications.
Wiping memory cards
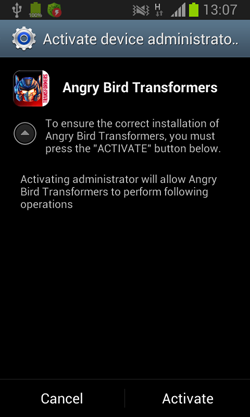
When launched, Android.Elite.1.origin requests access to administrative features of the mobile devices that are supposedly needed to complete the application's installation of the application. A corresponding message is displayed on the screen until the user agrees to perform the desired action (many Android-Android.Locker programs act in a similar fashion).
If successful, the malware will delete all the data from the SD card.
Working with SMS
Android.Elite.1.origin sends messages to all the contacts phone in the phone book in five second intervals. The message text is as follows:
HEY!!! [contact_name] Elite has hacked you.Obey or be hacked.
The malicious program blocks new message notifications to hide all incoming SMS messages. All received messages are placed into the inbox.
The program uses the method PhoneNumberUtils.isGlobalPhoneNumber() to check sender phone numbers of all received short messages against its list of cellular networks. If the number is validated, the message that reads Elite has hacked you.Obey or be hacked is sent to this number.
Blocking applications
The malicious applications checks every 0.5 second if any of the following programs is running:
- WhatsApp Messenger (com.whatsapp)
- Facebook (com.facebook.katana)
- Hangouts (com.google.android.talk)
- The default system SMS and MMS application (com.android.mms)
Should Android.Elite.1.origin find a window of any of these applications, the following image will be displayed on top of the program interface:
Thus, it makes using the application impossible.