Malicious application for Android that steals sensitive banking information from South Korean users. Distributed by attackers in the guise of the Google Play client application. When launched, it requests access to the device's administrative features, removes its icon from the application list on the home screen and notifies the user that an error has supposedly occurred and the program has been removed.
 |
 |
Steals banking security certificate
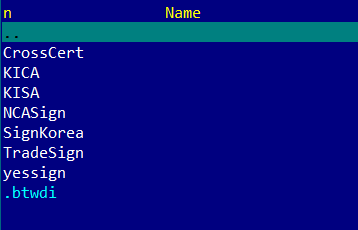
Then the program searches the memory card's root directory for the directory NPKI, which contains digital certificates that ensure the safety of financial transactions, and places its contents in a zip-archive, which is forwarded to the email-address jnohiugb[xxxxx]@gmail.com and uploaded to the server ml[xxx].iego.net using an embedded ajax-library.
Steals contact information and SMS messages
Also, the malicious application collects information about all the contacts in the phone book and puts the data into the file sdcard/phone001.txt. The file stores data in the following format:
number:"Example_phoneNumber";name:"Example_contact".In addition, all incoming short messages are placed in the separate file sdcard/temp/sms.txt. Messages are arranged in the file as follows:
name:"Example_name";phone:"Example_phoneNumber";content:"Example_content";date:"Example_date".Both of these files are uploaded to the intruders' server. In addition, all new incoming messages are also intercepted and forwarded to the criminals.
Steals banking authentication information
Android.Banker.28.origin checks whether the following programs are installed on the compromised device:
- com.shinhan.sbanking
- com.kbstar.kbbank
- com.hanabank.ebk.channel.android.hananbank
- nh.smart
- com.webcash.wooribank
- AhnLab V3 Mobile Plus 2.0
Information about all the applications found, as well as the phone number, is transmitted to a remote server.
At regular intervals, the Trojan checks whether one of the required banking applications is running and, if it is, the malware displays several messages and then imitates a dialogue prompting the user to enter their account information, which is then archived and forwarded to attackers.
 |
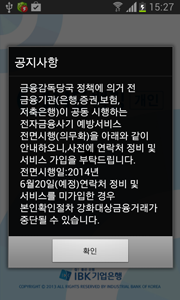 |
The requested information includes:
- clientId (IMEI)
- accountName
- accountNo (account number)
- accountPsw (password)
- bkType (bank name abbreviation)
- card (card number);
- transPsw;
- certPsw (certificate password)
- personIdFirst;
- personIdSecond.
To ensure its safety, Android.Banker.28.origin regularly checks the device for the presence of the anti-virus AhnLab V3 Mobile Plus. If the anti-virus is found, it is removed.
Control commands
Criminals can send various commands to the banker malware in SMS messages. In particular, the malware can receive the following directives:
- ak49 – send all the gathered information and change the target server (the new server address is specified as a corresponding command option).
- ak40 - enable or disable the forwarding of inbound SMS to a specified email (options "1" and "2" respectively).
- wokm - broadcast SMS messages to all available contacts (message text is specified as the command option).
- ak60 - change the email address to which the collected information is sent (the address is specified as a command option).
- ak61 - change the email account password (the password is specified as a command parameter).
The instruction wokm enables Android.Banker.28.origin to operate as an SMS worm (if the sent message contains a link to download the Trojan).
