Android.Locker.27.origin
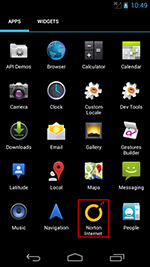
A ransomware Trojan that locks Android devices demanding a ransom to unlock them. It is distributed in the guise of an anti-virus program.
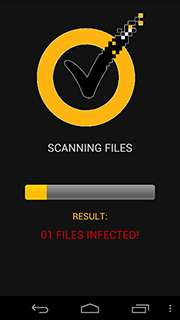
When launched, the Trojan imitates a scanning process, during which it detects 17 “threats”.
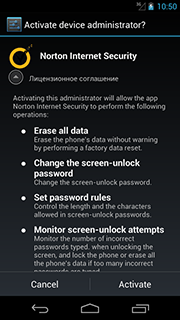
After that, Android.Locker.27.origin prompts the user to grant it administrator privileges.
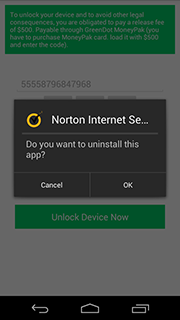
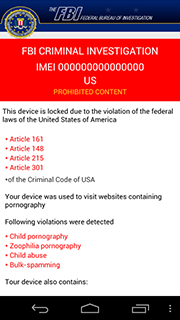
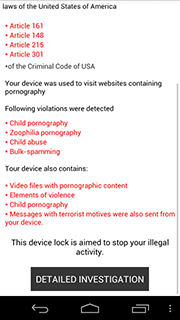
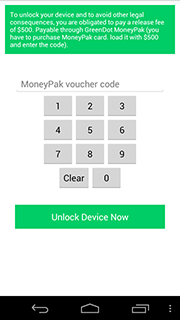
However, regardless of what action the user takes, the malicious program still locks the device displaying a warning about some violation of law. To unlock the device, the user has to pay a $500 ransom by loading a GreenDot MoneyPak card with the demanded amount of money and providing cybercriminals with the card code.
 |
 |
 |
If the victim attempts to close this message, for example, by pressing the Home button, Android.Locker.27.origin will repeat its request for administrator privileges (if the first attempt failed). After that, the Trojan will lock the device again.
Requirements for the entered code are as follows:
- The length should consist of 14 digits.
- The code must not contain such most predictable combinations as “00000”, “11111”, “22222”, “33333”, “44444”, “55555”, “66666”, “77777”, “88888”, “99999”, “12345”.
If these requirements are met and if there is an established Internet connection, Android.Locker.27.origin forwards the card code to cybercriminals' server at http://welcome[xxxxx].com/i2s9a2jx/api.php, deletes itself from the list of device administrators (if the user has granted the malware these privileges), and initiates its own removal.
If the requirements are not met, the Trojan displays an error message, and the device stays locked.
Thus, affected users can get rid of this threat by entering any 14-digit number that does not contain the mentioned combinations.