SHA1 hash:
- c96beb026dc871256e86eca01e1f5ba2247a0df6 (system.exe)
Description
A backdoor written in the C++ programming language and operating on computers running Microsoft Windows. Its main functionality is located in PowerShell code (PowerShell.BackDoor.108) that is encoded with Base64. Malicious actors control this malware via a Telegram bot by sending commands through it.
Operating routine
When launched, BackDoor.Siggen2.5463 assigns a DeviceID identifier to the infected computer. This identifier is a random number ranging from 100 to 10,000. Moreover, the malware executes a PowerShell command $env:COMPUTERNAME to obtain the infected device’s name.
Next, in an infinite loop, BackDoor.Siggen2.5463 requests commands from the Telegram bot whose address is hardcoded in the backdoor’s code. The results of executed commands, as well as messages about errors that occur, are sent to this bot.
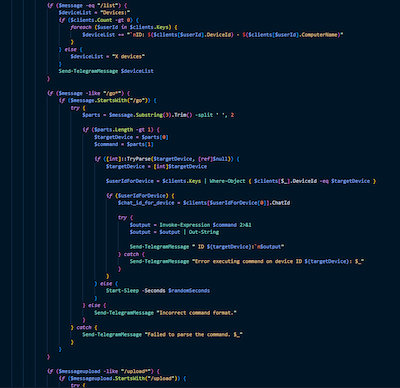
Supported commands are as follows:
- /list — to send the DeviceID and the computer’s name to the attackers;
- /go <DeviceID> <command> — to execute a specified PowerShell command with the commandlet Invoke-Expression.
Below are the commands that we observed:
- <file name>.exe — to run a specified file;
- ipconfig /all — to obtain information about the network configuration;
- netstat — to obtain information about current network connections;
- whoami — to obtain the user’s name;
- /upload <DeviceID> — to download a file to the infected computer and save it to C:\Users\Public\Libraries\%fileName%.
The BackDoor.Siggen2.5463 PowerShell code fragment responsible for executing commands