SHA1 hashes:
- 3e7e5de03e1e1cb472703602d5f8296e7aec3239 (the first modification discovered on 25.03.2021)
- 1d97a5ba869526433d09f315c4bb1c66dac7dddd (a modification discovered on 02.04.2021)
- 2ea82dcc114b75ce09a37a8f1b07675ca528d7c9 (an arm version, actual at the time of the analysis)
- a6490426bc4c94a70225285b94120c49b10e62d8 (x86 version, actual at the time of the analysis)
Description
An Android trojan built into the official APKPure catalog client software version 3.17.18. Its main functionality is to execute the malicious module hidden inside it. This module downloads other trojan components and loads various websites.
Operating routine
Android.Triada.4912 utilizes various techniques to protect itself from the analysis. Its code contains multiple garbage strings and has a large number of calls through the reflection. Moreover, the names of the methods and classes called through the reflection, as well as the strings of the malware are encrypted with an XOR operation with the d4as56fads4f4 key, and also in Base64.
The initialization of the trojan occurs in the ZcoupSDK class. For that, the following string is added to the initInternal method:
W1a3s4t9B0.Go(arg5.getApplicationContext(), "2021-3-22-ssk015-ym2", null, 1);
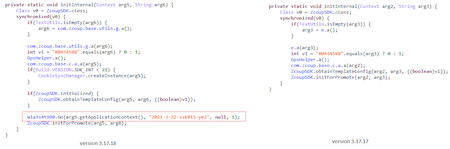
For comparison, the image below shows the corresponding code fragments of the trojanized version of the APKPure application and its original version:
The Android.Triada.4912 decrypts a payload (Android.Triada.566.origin) from the hardcoded string, placing the payload to the /files/*package_name*_s/ directory. It also decrypts the name of the main class of this malicious module, which is com.bb.s2x2e.go.AAA. After the successfully decrypting the payload, the trojan executes the initMe in it and loads the payload into the RAM.
In Android.Triada.4912, calls for the following methods from the payload are implemented through reflection:- initMe
- readData
- delayTime
- clickTime
- closeTime
- count
- chanEanble
- time
- setPackageName
- setSourceDir
- setPublicSourceDir
- getFBApk