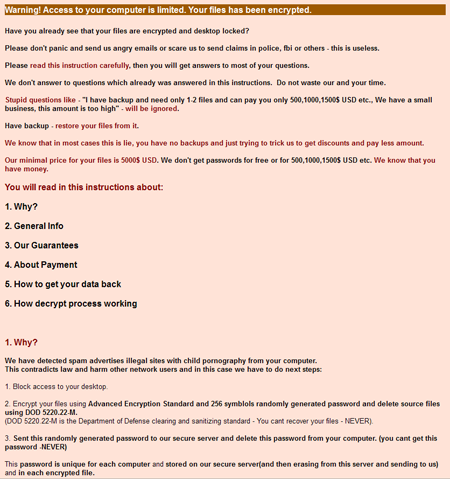
A multicomponent ransomware Trojan written in PureBasic and designed to encrypt files using WinRAR. Once the malware penetrates the system, it prevents the user from operating the machine by displaying a ransom demand.
After it is launched as a system service, the Trojan's encryption module creates numerous files, part of which serve the purpose of storing configuration data, information on paths to settings files, logs and executable files, and data regarding the infected computer. Then Trojan.ArchiveLock.20 empties the Recycle Bin, creates a list of files to be encrypted, and deletes existing backup copies. Using a special algorithm, the Trojan generates a list of passwords and launches the console version of WinRAR to place files from the compiled list into password-protected, self-extracting archives. The malware can encrypt more than 100 file types. By employing the Sysinternals SDelete utility, Trojan.ArchiveLock.20 deletes original files by overwriting them multiple times, which makes it impossible to restore those files.
While some files are encrypted using a simple password based on the hard drive serial number, other files are encrypted with a randomly generated password that can be more than 50 characters long. Names of the encrypted files are also modified using a special algorithm; for example, once encrypted, the picture.jpg graphics file will look as follows: picture.jpg(!! to decrypt email id 12345678 to sec****@gmail.com !!).exe.
Addresses provided by cybercriminals to their victims can include the following ones:
- sec777999@gmail.com,
- sec222555@gmail.com,
- sec333888@gmail.com,
- sec333888@gmail.com,
- ausec222999@gmail.com,
- sec777999@gmail.com,
- casec222777@gmail.com,
- auidhelp@gmail.com,
- sec777999@gmail.com,
- sec222555@gmail.com,
- sec333888@gmail.com,
- ausec222999@gmail.com,
- casec222777@gmail.com,
- auidhelp@gmail.com,
- usidhelp2@gmail.com,
- frsechelp@gmail.com,
- spainsec1@gmail.com,
- spainsec2@gmail.com.
If your computer has been infected with Trojan.ArchiveLock.20, do not attempt to reinstall the operating system or delete any files, because such actions can result in all the encrypted data being permanently lost. To decrypt the files, contact Doctor Web by submitting a ticket in the Request for Curing category.