Packer: absent
Compilation dates:
- 05.09.2018 05:38:37 (scansts.dll)
- 20.12.2018 16:08:02 (CLNTCON.ocx)
- 06.03.2019 06:58:28 (http_dll.dll)
SHA1 hashes:
- aa0e7101b1663c23f980598ca3d821d7b6ea342d (scansts.dll)
- b03c98a9539d4cbb17f2efc118c4b57882b96d93 (CLNTCON.ocx)
- d52152661c836e76bebd46046ba3f877c5d381d8 (http_dll.dll)
Description
A loader for BackDoor.PlugX.28 written in C. It is a malicious library that functions within the process of a valid executable file. This library unpacks and executes the shellcode with payload. The trojan utilizes DLL hijacking to load the malicious code into a process.
The loader’s components and the attacked applications:
| Executable’s SHA-1 hash | EXE | DLL | Shellcode |
|---|---|---|---|
| 5c51a20513ba27325113d463be9b5c6ed40b5096 | EMLPRO.EXE | scansts.dll | QuickHeal |
| b423bea76f996bf2f69dcc9e75097635d7b7a7aa | CLNTCON.exe | CLNTCON.ocx | CLNTCON.ocp |
| 5d076537f56ee7389410698d700cc4fd7d736453 | EHSrv.exe | http_dll.dll | ESETSrv |
Operating routine
scansts.dll
Once loaded to a process, the library transfers control to the call of scansts_2 the exported function by a hardcoded offset.
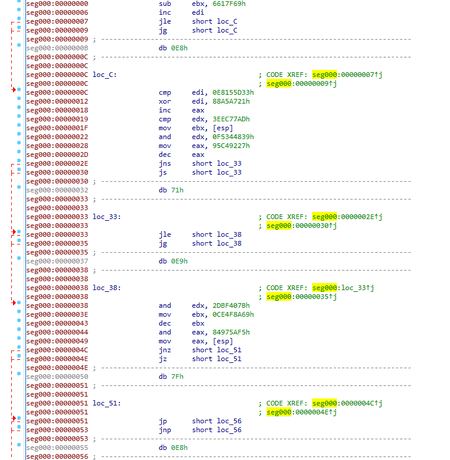
In that function the library refers to QuickHeal file, which is located at C:\Windows\System32 on the infected system. It then checks for the HKLM\Software\BINARY or HKCU\Software\BINARY registry key to determine further actions. If the registry keys are absent, the trojan initiates decryption of the QuickHeal shellcode and then calls it by passing it as an argument 0. Decryption algorithm:
s = ''
for i in range(len(d)):
s += chr((((ord(d[i]) + 0x4f) ^ 0xf1) - 0x4f) & 0xff)
CLNTCON.ocx
It is the improved version of scansts.dll. The main malicious code is located in the DllRegisterServer exported function. The function call decrypts the DLL’s code using an algorithm based on the XOR operation. The trojan then refers to CLNTCON.ocp and checks for the HKLM\Software\BINARY or HKCU\Software\BINARY registry keys. The shellcode is decrypted in two stages: in addition to the mentioned algorithm, the RC4 algorithm with the CLNTCON.ocp decoding key is also used.
http_dll.dll
It is equivalent to CLNCON.ocx except the following options:
- The main trojan’s code is located in the StartHttpServer exported function;
- ESETSrv is used as the RC4 decoding key.
QuickHeal shellcode
It is the obfuscated shellcode with an encrypted binary file and configuration. The obfuscated portion contains decryption instructions for the code that extracts the payload.
The payload is extracted by malmain function and defined by the following structure:
#pragma pack(push,1)
struct st_data
{
_DWORD size;
_BYTE data[size];
};
struct shellarg
{
_DWORD shellcode_ep;
_DWORD field_4;
st_data* mod;
_DWORD comp_size;
st_data* cfg;
_DWORD field_14;
_DWORD field_18;
};
#pragma pack(pop)RtlDecompressBuffer function is used for decompression. During the payload extraction process the shellcode verifies executable’s signatures. MZ and PE signatures are replaced with XV. Then DllMain is being executed. It receives the pointer to shellarg structure as a lpReserved parameter. This structure contains payload’s configuration.