The execution of the malicious code triggers a module that decrypts the Trojan's body. The module then loads code segments into the memory, configures import routines and transfers control to the entry point.
Then another module loads an image into the memory of the compromised machine.
Downloader
The Trojan downloader copies itself as %USER%\<rnd>.exe, and adds itself to the startup list:
software\microsoft\windows\currentversion\run <rnd>=%USER%\<rnd>.exe
It uses RSA keys to encrypt its traffic.
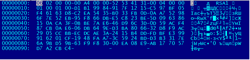
IAfter that a query encrypted with a public key is sent to a server:
It decrypts the reply with a private key:
The downloader incorporates a hardcoded list of domain names, some of which are encrypted too. It sends GET queries to domains on the list. In response, the Trojan obtains the main web page and parses the HTML code in search of the image tag <img src="data:image/jpeg;base64 … >.
It decodes tag arguments into a malicious file (upon a command or starts the process svchost.exe) and tries to inject the file code into the process, or saves it into a temporary folder.
Then it extracts a list of addresses and the module BackDoor.Bulknet.739 (DDoS) from its body and loads the module into the memory.
It sends an HTTP request to a server on the list, downloads a page and parses its HTML code in search of the image tag <img src="data:image/jpeg;base64 … >. It decrypts the tag arguments into a file disguised as a JPEG image. This file contains the data container, compressed with gzip. BackDoor.Bulknet.739 is decrypted from the compressed data.
Downloader routine
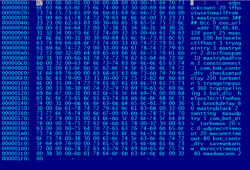
The downloader sends data in encrypted form. The encryption routine is as follows:
int crypt_send_data(DWORD *data, signed int size, int key1)
{
int count; // ecx@1
int key; // edi@4
int n; // eax@4
int size_add; // ebx@7
DWORD *v7; // esi@8
int v9; // [sp+4h] [bp-8h]@1
int v10; // [sp+8h] [bp-4h]@8
count = 0;
v9 = 0;
if ( data && size && key1 )
{
key = 0x19660D * key1 + 0x3C6EF35F;
n = size / 4;
if ( size / 4 > 0 )
{
v9 = 4 * n;
do
{
data[count] ^= key;
key = 0x19660D * key + 0x3C6EF35F;
++count;
}
while ( count < n );
}
size_add = size % 4;
if ( size % 4 )
{
v10 = 0;
v7 = &data[count];
memcpy(&v10, &data[count], size_add);
v10 ^= key;
memcpy(v7, &v10, size_add);
v9 += size_add;
}
}
return v9;
}
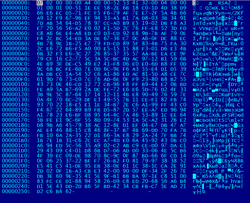
The packet structure:
struct HEAD{
uint32 rnd1;
uint32 rnd2;
uint32 crc32;
};
struct BOT_INFO{
uint32 field2;// 1
uint32 field3;// 2
uint32 field4;// 1
uint32 field5;// 0
uint32 field6;// 0
uint32 field7;// 15
uint32 rnd3[4];
uint32 bid[4];
uint32 instal_flag;
uint32 len_host_crc32;
uint32 host_crc32;
};
HEADER 0xC
97 73 BC F2 DB 00 76 E0 72 88 73 07
BOT_INFO 0x44
01 00 00 00 02 00 00 00 01 00 00 00 00 00 00 00
00 00 00 00 15 00 00 00 FA 13 29 40 56 6C 82 99
AF C5 DB F2 09 1F 35 4C 68 55 ED 52 F5 60 43 1E
1E 95 41 3A 33 21 C3 3B 0C 00 00 00 04 00 00 00
4B ED 16 27 00 00 00 00 00 00 00 00 00 00 00 00
DDoS
To mount DDoS attacks, the Trojan creates eight threads, picks a random address and sends a POST query to this address. The POST query:
http://%s/?ptrxcz_%s
or
http://%s/
The content and the string length are random. Also, once a connection to an SMTP server is established, the Trojan can send e-mails with arbitrary content via the server.
The bot saves itself into the folder % SYSTEM32% or %USERDIR% as regedit.exe and modifies the registry branch Software\Microsoft\Windows\CurrentVersion which is to be run at startup. It also modifies the registry branch SYSTEM\CurrentControlSet\Services\Tcpip\Parameters to increase the number of allowed TCP connections.
Spam machine
The Trojan uses a spam machine with a set of e-mail templates to send mass e-mails.
Mailing list:
A template containing a list of names:
If the Trojan process is terminated abnormally, it can generate and send a corresponding error report to a remote server via UDP.
Spam machine routine
All messages from the bot are sent as this data block:
struct MSG{
DWORD size;
BYTE data[size]; //encrypted data
};
The following routine is used for data encryption:
void ciper(char *key, char* data, int size){
uint32 max=sizeof(KEY_ENC)-1;
int j=0;
if ( key && data ){
if ( size > max){
do{
for (int i=0;i<max;i++){
data[i+j]^= key[i];
}
for (int i=0;i<max/2;i++){
char tmp = data[i+j];
data[i+j] = data[j-i+(max-1)];
data[j-i+(max-1)]= tmp;
}
if ( j & 1 ){
for (int i=0;i<max;i++){
data[i+j]=~data[i+j];
}
}
j+=max;
}while (j+max< size );
}
size=size%max;
for (int i=0;i<size;i++){
data[i+j]=~data[i+j];
}
}
}
Encryption and decryption keys:
0xe0:eto ochen prostoarelkioiqyrut
0xe1:turyqioikleraotsorp nehco ote
Outbound message structure:
struct HEAD_REQ{
DWORD bid;
DWORD lip;
DWORD bver;
DWORD num_cfg;
DWORD subop;
DWORD os;
WORD dns;
WORD smtp;
};
DWORD size;
//data in this field is encrypted
HEAD_REQ head;
BYTE data[size];
Inbound packets:
struct HEAD_RES{
DWORD cmd;
};
union U_OP{
OP_0 op0;
OP_1 op1;
OP_4 op4;
OP_5 op5;
OP_6 op6;
OP_7 op7;
OP_8 op8;
};
struct OP_0{
};
struct OP_1{
DWORD build;
DWORD size;
};
struct OP_4{
};
struct OP_5{
DWORD bid;
DWORD remote_addr;
DWORD seed_time;
DWORD d4;
};
struct OP_6{
DWORD num_tmpl;
DWORD d2;
DWORD d3;
DWORD num_x;
DWORD d5;
};
struct OP_7{
DWORD flag_op;
DWORD num_cfg;
};
struct OP_8{
DWORD sub_opcode;
BYTE b1;
};
enum OP_RES{
OP_0 = 0, //stop mailing, clear templates
OP_1 = 1, //list of name patterns
OP_4 = 4, //update the bot
OP_5 = 5, //bid initialization, determine the name of the compromised host
OP_6 = 6, //spam templates
OP_7 = 7, //main bot configuration file
OP_8 = 8, //mailing list
};
DWORD size;
//data in this field is encrypted
HEAD_RES head;
U_OP op;
BYTE data[size+sizeof(op)+sizeof(HEAD_RES)];
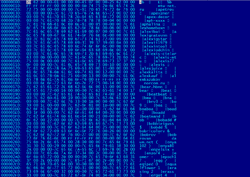
The Trojan sends packets in the following sequence:
- Outbound. The bid has not been initialized (if the bot is being launched for the first time). Contains a local IP lip, OS version, dns-flags, bot version bver, the number of tested SMTP servers. And num_cfg = 0
0x1C
00 00 00 00 C0 A8 EE 83 AC 01 00 00 00 00 00 00
00 00 00 00 05 01 28 0A 20 00 04 00 - Inbound. OP_7, contains the main configuration file for the spam machine.
0x1F1
07 00 00 00 01 00 00 00 08 00 00 00 75 64 70 73
6F 63 6B 63 6F 75 6E 74 00 32 30 00 69 66 68 6F
73 74 75 73 65 69 6E 6D 61 69 6C 66 72 6F 6D 00
31 00 6D 61 78 74 72 79 63 6F 6E 6E 00 33 23 23
23 23 00 62 63 63 00 30 00 65 78 65 5F 75 72 6C
00 00 61 64 64 72 00 37 38 2E 34 36 2E 34 36 2E
31 32 34 00 70 6F 72 74 00 32 35 00 6D 61 78 63
6F 6E 6E 00 31 30 30 00 68 65 6C 6F 73 65 6C 65
63 74 69 66 68 6F 73 74 00 33 00 74 72 79 61 67
61 69 6E 74 72 79 00 33 00 6D 61 78 74 72 79 65
72 72 00 32 00 64 69 65 69 66 6E 6F 73 70 61 6D
00 31 30 00 6D 61 78 74 72 79 62 61 64 66 72 6F
6D 00 32 00 63 6F 6E 73 74 63 6F 6E 6E 65 63 74
00 31 00 63 6F 6D 5F 62 6F 74 5F 63 6F 6E 74 72
5F 64 69 76 00 00 63 68 65 63 6B 73 6D 74 70 64
65 6C 61 79 00 32 35 30 00 74 75 72 62 6F 6D 69
6E 00 35 00 74 72 79 61 67 61 69 6E 70 61 75 73
65 00 33 36 30 00 74 72 79 70 69 70 65 6C 69 6E
69 6E 67 00 31 00 62 6F 74 5F 64 69 76 00 00 68
65 6C 6F 73 65 6C 65 63 74 69 66 6E 6F 68 6F 73
74 00 31 00 6B 6E 6F 63 6B 64 65 6C 61 79 00 36
30 00 6D 61 78 74 72 79 62 6C 61 63 6B 00 32 00
73 77 6F 74 74 69 6E 67 00 00 6D 61 78 75 64 70
74 72 79 00 35 00 63 6F 6D 5F 62 6F 74 5F 64 69
76 00 00 74 75 72 62 6F 6D 61 78 00 32 30 00 63
63 00 30 00 75 64 70 72 65 63 76 74 69 6D 65 6F
75 74 00 32 30 00 6D 78 63 6F 6E 6E 74 69 6D 65
6F 75 74 00 38 30 00 62 6F 74 5F 63 6F 6E 74 72
5F 64 69 76 00 00 73 61 76 65 75 6E 6B 61 6E 73
77 00 00 6D 78 72 65 63 76 74 69 6D 65 6F 75 74
00 38 30 00 6D 61 78 64 6F 6D 63 6F 6E 6E 00 32
00 - Outbound. num_cfg=head.num_cfg
0x1C
00 00 00 00 C0 A8 EE 83 AC 01 00 00 08 00 00 00
00 00 00 00 05 01 28 0A 20 00 04 00 - Inbound. OP_5, includes the bid, assigned to the bot, external IP of the compromised host and timestamp.
0x14The bot attempts to determine the host name for the external IP and sets a DNS flag.
05 00 00 00 97 68 1F 00 5F D3 A8 0A C8 E1 53 51
00 00 00 00 - Outbound. num_cfg = head.num_cfg, dns | 1 and the assigned bid will now be present in all packets.
0x1C
97 68 1F 00 C0 A8 EE 83 AC 01 00 00 08 00 00 00
00 00 00 00 05 01 28 0A 21 00 04 00 - Inbound OP_8. Mailing list
0x35
08 00 00 00 0B 00 00 00 00 50 41 59 56 45 53 55
50 50 4F 52 54 40 41 45 58 50 2E 43 4F 4D 00 77
70 70 69 6D 30 30 31 2E 41 45 58 50 2E 43 4F 4D
00 0C 0A DB 1A - Outbound. HEAD_REQ.subop=OP_8.sub_opcode, num_cfg=head.num_cfg
0x1C
97 68 1F 00 C0 A8 EE 83 AC 01 00 00 08 00 00 00
0B 00 00 00 05 01 28 0A 21 00 04 00 - Inbound. OP_6 spam template.
- Outbound. Similar to the previous one but contains more data.
struct OP_1_EXT{
DWORD field4;
DWORD field5;
DWORD field6;
DWORD field7;
DWORD field8;
};0x1C
97 68 1F 00 C0 A8 EE 83 AC 01 00 00 08 00 00 00
0B 00 00 00 05 01 28 0A 21 00 04 00
OP_1_EXT.field4=OP_6.num_tmpl;
OP_1_EXT.field5=OP_6.d2;
OP_1_EXT.field6=HEAD_REG.num_cfg;
- Inbound. OP_1 list of names.
And OP_1.num_tmpl==OP_6.num_tmpl template number.