SHA1:
- 6d0c88f488902d0c975167068027920ca18ff8af
- a305a0f363bc8891ca7a5ca31e20c2c01b5a6c24
- 70e39daafe8d68ec2b43b3ce7353e5364a381ba2
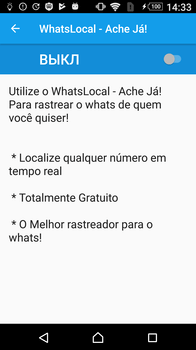
A Banking Trojan for Android mobile devices. Its main goal is to steal confidential data. Android.BankBot.495.origin was first detected on Google Play and attacked Brazilian users. The Trojan was distributed under the guise of applications intended for spying on the owners of mobile devices.
How it starts
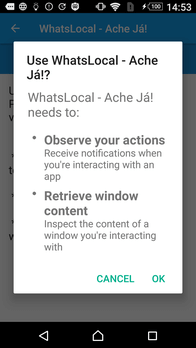
When launched, Android.BankBot.495.origin opens system settings and prompts the user to permit it to access the Accessibility option. If a potential victim agrees to do it, the Trojan may read the contents of the active application windows and tap buttons independently of the user.
Having obtained the permissions, Android.BankBot.495.origin launches MainService and automatically closes the accessibility settings window.
Then the malware tries to obtain the privileges needed to show overlay windows and forms. For that, it requests the following permission in the system:
- android.permission.ACTION_MANAGE_OVERLAY_PERMISSION
If the system language on the mobile device is Portuguese, the Trojan automatically taps the “PERMITIR” buttons and obtains the necessary privileges by itself.
How initial settings are obtained
The MainService starts the Main2Activity, which loads the address http://brazilian*****.ddns.net/renew in an invisible WebView window. Next, the website executes a chain of redirections:
- http://brazilian*****.ddns.net/renew
- http://brazilian*****.ddns.net/renew/
- http://brazilian*****.ddns.net/renew/1.php?cg=MzQuM******2LjgyfDUyLjEyL******2OA==]
- http://brazilian*****.ddns.net/renew/d.html?finishurl
The key 1.php?cg= signals the Trojan that the link contains the settings it needs, i.e. the addresses of the main command and control servers encoded in Base64. The ] symbol is the closing key for the encoded data. After decryption, the addresses of the remote hosts are as follows:
34.222.**.**|52.12.**.***
The first IP address belongs to a server with fraudulent web pages that the Trojan will use for phishing attacks. The second address belongs to the command and control server of the Trojan.
After successfully accepting the settings and receiving the ?finishurl key in the last link, the Trojan terminates the Main2Activity.
Receiving the commands and using accessiblity features to steal confidential data
When launched, MainService starts two permanently active threads, ProcessualThread and AppStartWatchThread. ProcessualThread sends queries to the command and control server at http://52.12.**.***/mobileConfig.php every 6 seconds and executes the commands it sends back. The process is as follows.
-
The Trojan executes a query with the parameters
hwid=********3X37a********681bf&type=1&act=firstRun (where hwid is a device identifier that contains the serial number of hardware and Settings.Secure.ANDROID_ID). In response, the Trojan receives JSON with a list of applications. Android.BankBot.495.origin checks whether these applications are installed on the mobile device and sends the result in the following query:hwid=********3X37a********681bf&ttdd=%5B%22oct2%22%5D -
The Trojan executes a query with the parameters
hwid=********3X37a********681bf&operador=cfData&content=chkItTk. If the server response contains the string “mobile_ita_tk”, the Trojan launches the Banco Itaú (com.itau) application. Next, it reads the contents of its window, saves, and transmits the data on the balance of the victim’s bank account to the server. Then it taps the buttons “alterar conta”, “acessar com outra”, as well as “iToken”, by itself. After that Android.BankBot.495.origin sends the contents of the application interface element with the text “Número válido por” (the iToken key value) to the server. -
The Trojan executes a query with the parameters
hwid=********3X37a********681bf&operador=cfData&content=chkDescoTk. If the server response contains the string “mobile_desco_tk”, the Trojan launches the Bradesco (com.bradesco) application and tries to enter the PIN code received in the command. Then Android.BankBot.495.origin uses the accessibility feature to analyze the contents of the app window and perform the following steps, depending on the interface element:- if the string representation contains “viewIdResName: agn”, the Trojan stores it to the Agencia variable;
- if the string representation contains “viewIdResName: ctaDig”, Android.BankBot.495.origin stores it to the Conta variable;
- if the window contains an element with the text “CHAVE DE”, and the server sends a command to launch the compromised application, the Trojan taps this element and checks the box to indicate that the button has been tapped;
- if the checkbox that corresponds to the “CHAVE DE” button is active, and the window contains an element titled “DIGITAR A SENHA”, the Trojan taps it;
- if the checkbox that corresponds to the “CHAVE DE” button is active, and the window contains an element titled “Digite seu PIN”, Android.BankBot.495.origin enter the PIN code received from the server and checks the box to confirm that password has been entered;
- if the box indicating that PIN code has successfully been entered is checked, and the element contains the description “OK”, the Trojan taps it;
- if the window element description contains the string “valorSaldoBox”, Android.BankBot.495.origin stores its value to the Saldo variable;
- if the element description contains “id/otp_field”, the Trojan stores its string representation as “Token”.
- Contents of the variables Agencia, Conta, Saldo, and Token are uploaded to the server http://52.12.**.*** in the thread AppStartWatchThread.
-
Then the Trojan executes two queries:
- hwid=********3X37a********681bf&operador=cfData&content=chkSMSB;
- hwid=********3X37a********681bf&operador=cfData&content=chkSMSCf.
If the server response contains the string “chkSMS”, the Trojan launches the default SMS application. Using the accessibility features, Android.BankBot.495.origin, reads and saves the messages stored in this application.
Data collected by the Trojan is sent to the server in the thread AppStartWatchThread, which constantly monitors the changes in the class variables. Android.BankBot.495.origin also recognizes the messages from CaixaBank S.A. and sends them to the server in a separate request.
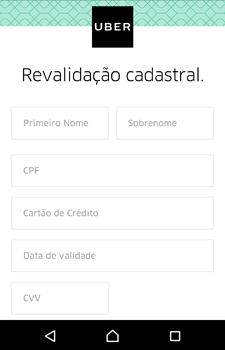
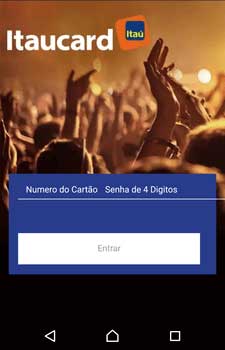
Phishing attacks
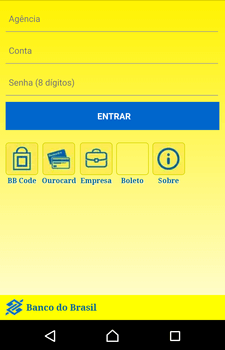
Android.BankBot.495.origin uses the accessibility features to track the activities of the following apps:
- Itaucard Controle seu cartão;
- Banco do Brasil;
- CAIXA;
- Bradesco;
- Banco Itaú;
- Uber;
- Netflix;
- Twitter.
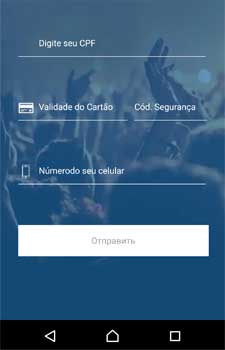
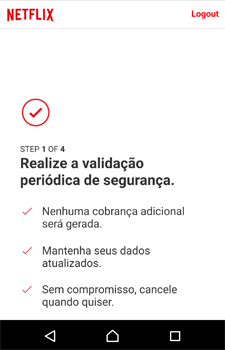
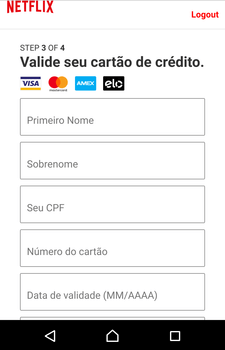
When one of them is launched, the Trojan displays an overlay WebView window with a phishing webpage, received from the command and control server 34.222.**.**. The page imitates the compromised software and requests that the user fills in confidential information: logins, passwords, account names, bank card details, etc. After entering and sending the data, the fraudulent page redirects to a link with the string “finishurlkk”. Android.BankBot.495.origin then closes the WebView window and re-launches the app, so as not to arouse suspicion if the target application was closed or collapsed.
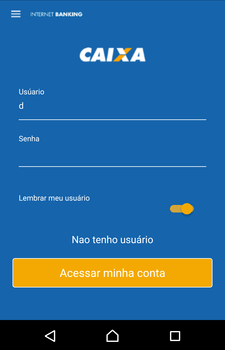
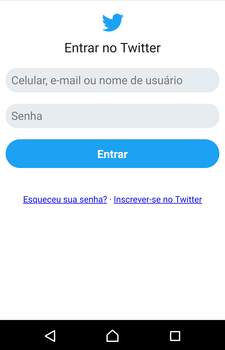
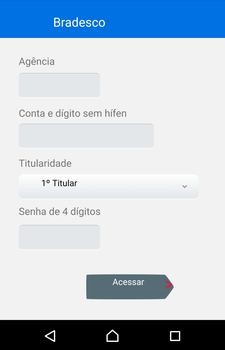
Fraudulent input forms the Trojan can display:
Self-protection mechanism
Android.BankBot.495.origin has a self-defense mechanism. The Trojan controls the startup of applications and searches the package names for a match in the following lines:
- com.vtm.uninstall
- com.ddm.smartappunsintaller
- com.rhythm.hexise.uninst
- com.GoodTools.Uninstalle
- mobi.infolife.uninstaller
- om.utils.uninstalle
- com.jumobile.manager.systemapp
- com.vsrevogroup.revouninstallermobi
- oo.util.uninstall
- om.barto.uninstalle
- om.tohsoft.easyuninstalle
- vast.android.mobile
- avast.android.cleane
- om.antiviru
- om.avira.andro
- om.kms.fre
If a match is found, it taps the “Back” button 4 times in an attempt to close the program.