SHA1:
- c71a842d93d04524d4df3f306c5d1d6ebc3c3bc7
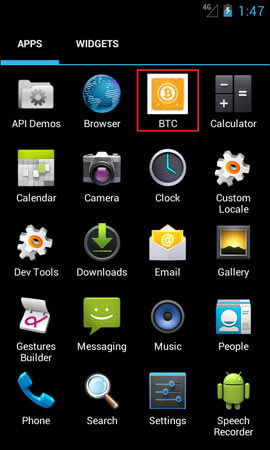
A malicious program for Android mobile devices. It can be distributed under the guise of popular harmless applications, such as software for the Bitcoin cryptocurrency:
When Android.Clipper.1.origin launches for the first time, it makes its main activity clipper.abcchannelmc.ru.clipperreborn.MainActivity inaccessible by changing the access settings. As a result, the malicious application’s icon disappears from the list of programs on the Android home screen.
In the OnPrimaryClipChangedListener interface, the Trojan then adds a listener that tracks changes in the clipboard content and waits for a user to copy a number of one of the targeted digital wallets.
Once the corresponding number is found in the clipboard, Android.Clipper.1.origin sends the number information to the http://fastfrmt.*****.tech command and control server. The malware then reconnects to the server and waits for the cybercriminals’ wallet number that belongs to the same payment system as the intercepted number.
The Trojan tracks and replaces wallet numbers of the following payment systems and cryptocurrencies:
- QIWI
- WebMoney R
- WebMoney Z
- Yandex.Money
- Bitcoin
- Monero
- zCash
- DOGE
- DASH
- Etherium
- Blackcoin
- Litecoin
To provide the autostart every time the infected mobile device is turned on, Android.Clipper.1.origin tracks the following system events:
- android.intent.action.BOOT_COMPLETED;
- android.intent.action.QUICKBOOT_POWERON;
- com.htc.intent.action.QUICKBOOT_POWERON.