SHA1:
- 733bd736d2a6c3cf1eca307ca16a5d2236403bc1
The following modification of Trojan.PWS.Stealer.21284 is completely rewritten in С++. Its self-designation is “Kratos”.
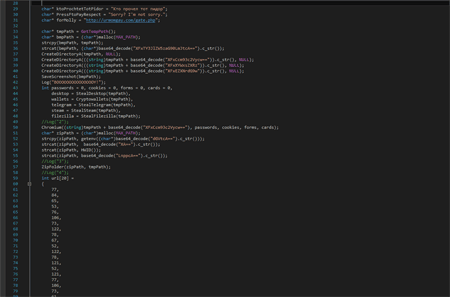
The majority of functions starts with the insertion written in Assembly that checks the flag BeingDebugged in PEB. Part of the strings is encoded using base64.
The main logic of the Trojan’s operation is shown in the following figure:
Once launched, the Trojan saves a screenshot to the file %TEMP%\\Screenshot.bmp, then it creates folders “%TEMP%\\Browsers”, “%TEMP%\\Wallets” and “%TEMP%\\Desktop”.
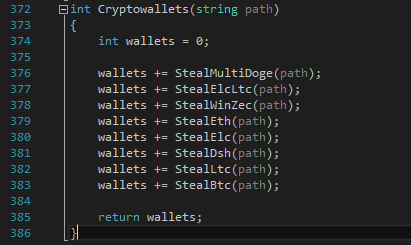
It copies to the folder “%TEMP%\\Desktop” all files with extensions TXT, DOC, DOCX and LOG found on the Desktop (walk through the Desktop is not recursive). Then it consecutively tries to find wallet files of different cryptocurrencies. Once the wallets are detected, the Trojan copies them to the folder “%TEMP%\\Wallets”:
Then it makes attempts to find the Telegram files on a computer, all while checking only the contents of the folder “%AppData%\\Telegram Desktop\\tdata”. The Trojan searches for files that contain values “D877F783D5D3EF8C” and “map” in their names. The detected files are copied into the folder “%TEMP%\\Telegram\\”.
The malicious program tries to determine the path to the installation folder of the gaming client Steam using the system registry key [HKCU\\Software\\Valve\\Steam] "SteamPath". Once Steam is detected, the stealer copies files “config\config.vdf", "config\loginusers.vdf", "config\SteamAppData.vdf” and saves them to the folder “%TEMP%\\Steam”.
Then the Trojan checks the availability of the file “%AppData\\FileZilla\\sitemanager.xml” and upon detection copies it into the folder “%TEMP%\\FileZilla”.
The Trojan steals confidential data, including cookies files, saved passwords, autofill data (including banking card numbers) from browsers and saves them to the folder “%TEMP\\Browsers”.
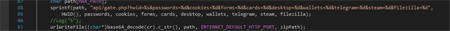
Then the obtained data is packed in to an archive and sent to the command and control server using the POST request.