SHA1:
- 4ae16eb89144b06e91c43b8c1fbcf4e07a2c13ef
- 359e073544599a0038977b41a98b5e98dca9511d
A Trojan for Android mobile devices. It was distributed on Google Play under the guise of popular harmless applications.
Once launched, Android.Click.245.origin establishes a connection with the command and control server by sending the following request:
GET http://vkapi.ru/vk/board.php HTTP/1.1
Host: vkapi.ru
Connection: Keep-Alive
Accept-Encoding: gzip
User-Agent: okhttp/3.3.0
Proxy server checks the IP address of the infected device. Depending on the user’s country, the server sends the Trojan a link to a particular website that must be loaded. The link is loaded using WebView. If Android.Click.245.origin does not receive the task, it downloads several pictures from the Internet and displays them on the screen.
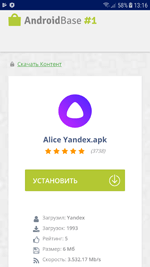
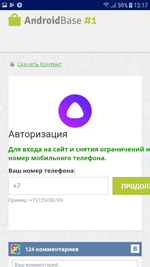
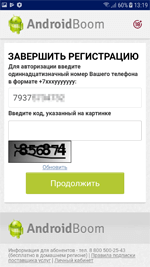
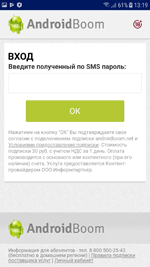
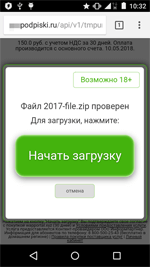
If the device is connected to the Internet via Wi-Fi, the user is invited to download an application on the website’s page. To do this, the user is asked to enter his phone number to receive a confirmation code via SMS. Upon entering the code, the victim is subscribed to an expensive service of one of the content providers rather than receiving the intended application.
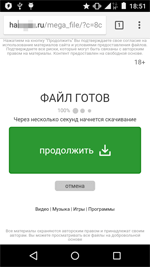
If the Internet access is provided via a mobile connection, the loaded website makes several redirections. The Trojan then finally opens the website in Google Chrome. On this website, the user is also invited to download an application. In this case, however, there is no need to enter phone numbers for receiving SMS confirmation codes. The subscription to a premium content service provider is executed automatically using the Wap-Click technology upon clicking the “Start download” or “Download” buttons.