SHA 1:
- 24f4f3c8586877d26a7f04b54a8f05398d8ff3c5
A Trojan program intended for mining cryptocurrencies. It is installed on servers run on Microsoft Windows Server using a vulnerability in Cleverence Mobile SMARTS Server via the RDP protocol.
It is a dynamic library (DLL) having 5 exports:
1 .00000001`800029D0 Install
2 .00000001`80001690 ServiceMain
3 .00000001`800025C0 Stealth
4 .00000001`80001F40 Test
5 .00000001`80002DD0 Uninstall
Having the unauthorized access to the server, cybercriminals save the library to the directory %TEMP% and run it using rundll32:
2017-Jul-19 10:33:07.011857 [5320] [INF] [1600] [arkdll]
id: 49444, timestamp: 10:33:07.011, type: PsCreate (16), flags: 1 (wait: 1), cid: 8380/10700:\Device\HarddiskVolume2\Windows\System32\cmd.exe
source context: start addr: 0x7ff64f886e20, image: 0x7ff64f880000:\Device\HarddiskVolume2\Windows\System32\cmd.exe
created process: \Device\HarddiskVolume2\Windows\System32\cmd.exe:8380 --> \Device\HarddiskVolume2\Windows\System32\rundll32.exe:12920
bitness: 64, ilevel: high, sesion id: 15, type: 0, reason: 1, new: 1, dbg: 0, wsl: 0
curdir: C:\Windows\system32\, cmd: rundll32 Inject.dll,Stealth SPB06
status: signed_microsoft, system_file_host, spc / signed_microsoft / clean
id: 49444 ==> allowed [2], time: 0.739863 ms
Export Install
In the Windows Server system registry, it creates the key [HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Svchost], saves the string "WdiServerHost” to the field “netsvcs”; the string is then used as the name of the Trojan service. It creates the service "WdiServerHost” with the displayed name “Diagnostic server host” and the following description:
The Diagnostic server host is used by the diagnostic policy service to host diagnostic tools run in the local system. If this service is stopped, some diagnostic tools, which depend on this service, will not function.
The service is launched automatically, "%%SystemRoot%%\system32\svchost.exe -k netsvcs” is specified as the executed file. Then, using the system registry branch "%%SystemRoot%%\system32\svchost.exe -k netsvcs” and the parameter “ServiceDll” the Trojan writes its name as the library loaded by the service. For the "ServiceDllUnloadOnStop” parameter, the value “1” is set, and then the service is run.
Export Stealth
It gets privileges "SeBackupPrivilege" and "SeRestorePrivilege". It reads the value of the "netsvcs” parameter of the system registry key [HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Svchost]. If the value is empty, it finishes.
It scans the system services listed in "netsvcs” to find a service with the launch type set as SERVICE_DEMAND_START or SERVICE_DISABLED. If the required service is found, it copies the creation, change and access time of the file indicated in the service ServiceDll, deletes the original file of the service and replaces it by its own copy setting the creation, change and access time as in the original file. It saves the input parameter in “ServiceWorker”. Then, it sets the automatic start for the service and runs it.
Export ServiceMain
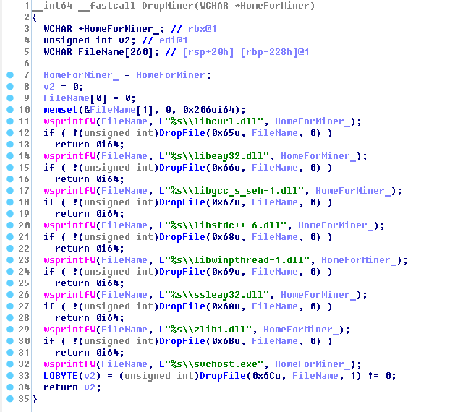
It gets the "SeDebugPrivilege” privilege. It gets the address of the function "NtSetInformationProcess” from ntdll.dll and sets the critical flag for its process. It seeks a disk with the DRIVE_FIXED parameter and selects the first directory on it. If the directory name in the lowercase does not match “$recycle.bin”, it extracts files from its own resources and saves them to this directory:
It gets the "SeDebugPrivilege” privilege. It gets the address of the function "NtSetInformationProcess” from ntdll.dll and sets the critical flag for its process. It seeks a disk with the DRIVE_FIXED parameter and selects the first directory on it. If the directory name in the lowercase does not match “$recycle.bin”, it extracts files from its own resources and saves them to this directory:
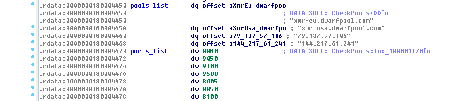
If there is at least one running server, the Trojan runs the miner stored in the svchost.exe file with the following parameters:
-t %d -a cryptonight -o stratum+tcp://%s -O 4JUdGzvrMFDWrUUwY3toJATSeNwjn54LkCnKBPRzDuhzi5vSepHfUckJNxRL2gjkNrSqtCoRUrEDAgRwsQvVCjZbS15Y5w6TATZ1WR7Tke.%s:x
Parameters are as follows:
- Number of kernels;
- Runing server’s address;
- The string saved in the ServiceWorkers parameter of the Trojan service.
The string saved in the ServiceWorkers parameter of the Trojan service.
Export Test
It performs the same actions as Export Stealth, but replaces with its copy not one service, but all services that match the set parameters.
Export Uninstall
It deletes the "WdiServerHost” service.
Curing
Since the Trojan replaces one of the Windows Server system services, it is cured in several stages.
- Scan the infected server using the Dr.Web Antivirus or the Dr.Web CureIt! utility and confirm the suggestion of the antivirus to cure infected files.
- Restart the server. To recover the system library deleted by the Trojan, run the following command in the console:
sfc /scannow
- Restart the server again.
- Install security updates released by the Cleverence Mobile SMARTS Serve developer, which cover the vulnerability of the application.
- It is recommended that the outside network access to the Cleverence Mobile SMARTS Server software is restricted.
- Change passwords for all user accounts on your server.