SHA1:
- ca2e7c66b9eedf95f51204cea8cd2e13ba2a5d93
- d72ca5ca1e7dc6431c041bfc6d7e3f9bfa39959c
A ransomware Trojan that infects Android mobile devices. It is distributed among Chinese users under the guise of benign programs.
Once launched, Android.Encoder.3.origin removes its shortcut from the program list on the device home screen, changes the home screen wallpaper for its own, and after that encrypts files on an SD card using the AES algorithm. For this purpose, the Trojan generates a random number used for generation of an encryption key. The encrypted files get an extension that looks the following way: “.勿卸载软件解密加QQ1951275599bahk[generated number]”.
Android.Encoder.3.origin does not encrypt a file if:
- a file name starts with “.”;
- a file is located in folders “android”, “DCIM”, “download”, “miad”, “com.”;
- a file size is less than 10 KB.
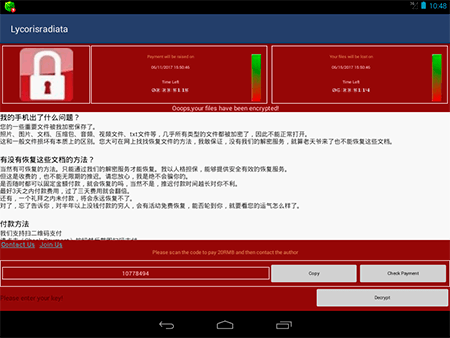
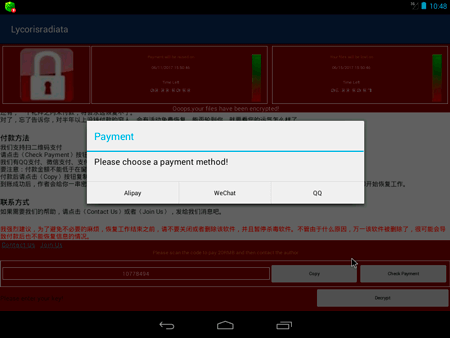
After the encryption, the Trojan displays a message, which orders a user to pay a ransom of 20 yuan. This message looks the same as a notification of the WannaCry Trojan (Trojan.Encoder.11432); however, these malicious programs are not interrelated. Authors of Android.Encoder.3.origin just used a known image.
Every three days the ransom doubles. If the user does not pay cybercriminals within a week, Android.Encoder.3.origin deletes the encrypted files.
Restoration of files affected by this Trojan is possible. For this purpose, users should contact Doctor Web’s technical support and provide a sample of an encrypted file. For users who have purchased commercial licenses for Dr.Web products, decryption service is available for free.