SHA:
- ab73d81c5c517a422dbb6fd3eac72d3442c3f5b6
- 92d664954750cb4c2f4ee9cb2943abbecbfc8204
- 9b2608626225e8daf58ca38565dd3bab401b07d7
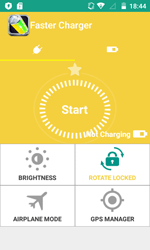
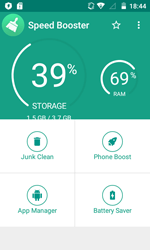
A Trojan for Android that is spread under the guise of benign programs, e.g., optimizing utilities. Several known modifications of Android.Click.132.origin were available for download from Google Play.
When launched, Android.Click.132.origin receives the addresses of web resources with advertising from the command and control server. Then the Trojan creates a hidden WebView window with the size of 1024×1800 pixels and opens the specified websites there. Android.Click.132.origin locates the advertisements and links on the loaded page on the basis of the coordinates specified by the server and automatically clicks on the advertising objects, simulating user actions. As a result, the cybercriminals make profit.
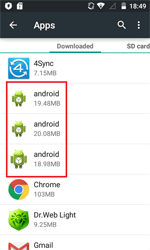
In a period of time after the installation, Android.Click.132.origin could delete its shortcut from the home screen of the operating system, in order to hide its presence on the infected device. However, the information about the Trojan is still present in the system program list that specifies it as an application under the name of android.
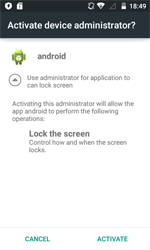
Android.Click.132.origin prompts the user to grant it administrative privileges to hinder its removal from the system.