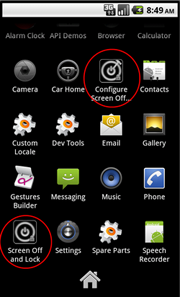
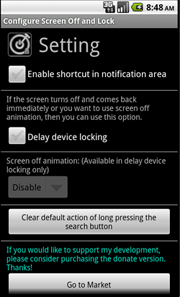
A Trojan for Android mobile devices. It is distributed through popular Chinese sites offering free software for Android. The malicious code is incorporated into a legitimate application called “Screen Off And Lock”.
 |
 |
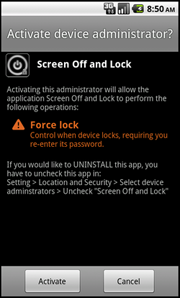 |
Once the infected program is launched, the backdoor establishes a connection to the remote server and awaits further commands. The Trojan can stealthily download and install different applications specified by cybercriminals. Using CHMOD and the “pm install –r” command, Android.Anzhu can change an application’s system privileges and covertly install it (only if root access is available).
Moreover, the Trojan can add bookmarks in several most popular browsers for Android. The backdoor does not simply add bookmarks specified by cybercriminals. It changes their attributes marking them as “visited” to make the user believe they have already visited those resources.
Android.Anzhu is able to read data from the Android system log monitoring events related to the launch and opening windows of other applications. The Trojan can also gather various device-related information (for example, the list of installed applications, IMEI, mobile phone number, and other) and send it to cybercriminals.
