SHA1: c829db3e169a67f1e623f2355a0935bc89c16c64
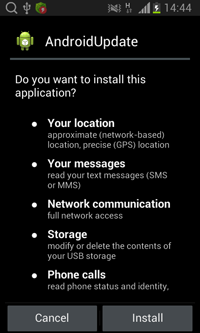
A Trojan designed to spy on Chinese users. It is distributed under the name of “AndroidUpdate”.
When launched for the first time, the Trojan extracts the following additional components from its body:
- super,
- detect,
- liblocSDK4b.so,
- libnativeLoad.so,
- libPowerDetect.cy.so,
- 1.dat,
- libstay2.so,
- libsleep4.so,
- substrate_signed.apk,
- cInstall.
Next, it tries to run the cInstall module (Android.BackDoor.41) with root privileges. If the Trojan does not succeed in acquiring root privileges, then the module is run without them.
If the attempt is successful, cInstall installs the “super” module into /system/bin and libnativeLoad.so and liblocSDK4b.so into /system/lib. Moreover, it stealthily installs the substrate_signed.apk application on the system.
Then the Trojan removes its shortcut from the Home Screen and launches the malicious service called PowerDetectService that monitors the following system events:
- android.intent.action.BOOT_COMPLETED (boot is completed),
- android.net.conn.CONNECTIVITY_CHANGE (network connectivity change).
Moreover, PowerDetectService runs the substrate_signed.apk module responsible for intercepting data entered by the user.
In addition to that, PowerDetectService communicates with the libnativeLoad.so library (Android.BackDoor.42) that runs the “detect” file (Android.BackDoor.45). This executable file, in turn, activates the libsleep4.so library (Android.BackDoor.46) that constantly takes screenshots and intercepts data entered by the user and the libstay2.so library (Android.BackDoor.43) whose purpose is to steal contact list data and monitor SMS messages and messages exchanged via QQ.
The 1.dat component can receive a number of commands from the command and control server—among them are the following ones:
- DOW—download a file form the server
- UPL—upload a file to the server
- PLI, PDL, SDA—update malicious modules and settings
- DIR—get the list of files residing in the specified folder
- DTK—write the contents of the specified folder into a file
- OSC, STK—run a search for the specified file of folder
- OSF—abort the search of the specified file
- DEL—delete the specified file
- SCP—take a screenshot
- BGS—activate the microphone and start recording
- GPRS—start tracking GPS coordinates
While some commands are executed by the 1.dat module on its own, other commands are carried out with the help of other malicious libraries that closely communicate with each other through UNIX sockets using double-byte commands:
Commands executed via /data/data/com.sec.android.service.powerManager/cores/audioListener
- 0x2633—start recording using the built-in microphone,
- 0x2634—stop recording,
- 0x2635—update the configuration file to record audio.
Commands executed via /data/data/com.sec.android.service.powerManager/cores/smsListener
- 0x2629—copy the contact list,
- 0x2630—copy the contact list,
- 0x2631—copy SMS messages,
- 0x2632—copy the call log.
Command executed via /data/data/com.sec.android.service.powerManager/cores/location
- 0x2628—forward information on the device's location to cybercriminals.
Command executed via /data/data/com.sec.android.service.powerManager/cores/location
- 0x2532—forward information on the process name of the currently used application.
Command executed via /data/cores/Users/All Users/Intel/Data/plugin2IPC
- 0x2678—upload the data entered by the user to the server.
To get the infected device's GPS coordinates, the Trojan uses Baidu Maps for Android. All data gathered by the malware is stored locally on the compromised device. When necessary, cybercriminals can acquire it using the mentioned commands (UPL, DIR, and so on).
The libPowerDetect.cy.so module (Android.BackDoor.39) logs entered text by intercepting the following methods:
- android.view.inputmethod.BaseInputConnection.commitText(CharSequence text, int newCursorPosition)
- android.inputmethodservice.InputMethodService.onFinishInput()
- android.inputmethodservice.InputMethodService.onWindowHidden()
To intercept methods, MSJavaHookMethod from Tool.Substrate.1.origin is used.