Virus library
An analysis of the technologies used by cybercriminals allows us to draw conclusions about the virus industry’s possible vectors of development and more effectively confront future threats. You, too, can learn what actions various malicious programs take in infected systems and how to withstand them.
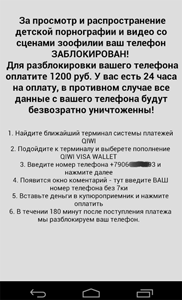
Android.Locker.139.origin in virus library:
A family of ransomware Trojans for Android.
Different modifications of these malicious programs can lock the device displaying a warning about some violation of law. To unlock the device, the user has to pay a ransom. If the user attempts to close the warning message or to exit to main menu, the message reappears preventing the user from operating the device in a usual way.
More dangerous modifications of Android.Locker run a search for user files stored on an SD card (for example, graphics files with .jpeg, .jpg, .png, .bmp, .gif extensions, text files with .pdf, .doc, .docx, .txt extensions, video files with avi, .mkv, .3gp extensions) and encrypt them. Then Trojans demand a ransom to unlock these files.
If you have encountered the first modification of these Trojans, it is recommended to reboot the device in safe mode (see User Manual) and to remove the malware manually or using Dr.Web for Android.
Vulnerabilities for Android
According to statistics, every fifth program for Android contains a vulnerability (or, in other words, a "loophole") that lets cybercriminals successfully introduce Trojans onto mobile devices and manipulate them into doing whatever actions they need them to.
Dr.Web Security Auditor for Android diagnoses and analyses a mobile device’s security and offers solutions to address security problems and vulnerabilities.