Virus library
An analysis of the technologies used by cybercriminals allows us to draw conclusions about the virus industry’s possible vectors of development and more effectively confront future threats. You, too, can learn what actions various malicious programs take in infected systems and how to withstand them.
Android.Dendroid.1 in virus library:
Trojans that belong to the class of Remote Administration Tools (RAT). These malicious programs are designed to target Android devices. They can be incorporated into any Android application, which makes their distribution rather easy.
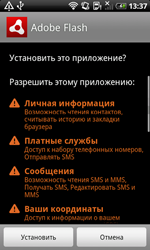 | 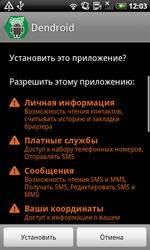 |
These Trojans can execute a number of commands, for example, the following ones:
- Intercept and block SMS messages
- Activate the device camera and microphone
- Get information on browsing history and bookmarks
- Get information on user accounts and contacts
- Send SMS messages
- Make phone calls
- Record phone calls
- Get files stored on the device
- Carry out a DDoS attack on specified websites
- Track GPS coordinates
- Display different dialog windows
- Launch applications
- Open specified webpages and follow specified links
- Delete files
- Update itself
Vulnerabilities for Android
According to statistics, every fifth program for Android contains a vulnerability (or, in other words, a "loophole") that lets cybercriminals successfully introduce Trojans onto mobile devices and manipulate them into doing whatever actions they need them to.
Dr.Web Security Auditor for Android diagnoses and analyses a mobile device’s security and offers solutions to address security problems and vulnerabilities.
