Virus library
An analysis of the technologies used by cybercriminals allows us to draw conclusions about the virus industry’s possible vectors of development and more effectively confront future threats. You, too, can learn what actions various malicious programs take in infected systems and how to withstand them.
Android.Bodkel.123 in virus library:
A family of malicious programs for Android that employ code obfuscation.
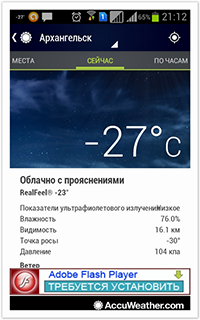
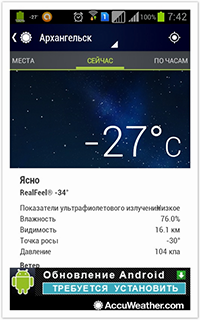
They are distributed with the help of advertising messages displayed in legitimate applications downloaded from various sources, including Google Play.
Usually, Trojans belonging to the Android.Bodkel family are disguised as update packages. However, they can also be distributed as games, Flash players, or applications for saving battery power.
When launched, these malicious programs prompt the user to grant them administrative privileges. If this attempt is successful, Trojans remove their shortcuts to conceal themselves from the user. If the attempt fails, these malicious programs will continue to prompt the user to grant them higher privileges until they succeed.
The main purpose of these malicious applications is to steal data from the user's contact list and to covertly send SMS messages. Moreover, Trojans of the Android.Bodkel family upload to the remote server at xx.xx.115.154 various device-related information (IMEI, mobile network operator, OS version, installed applications, and other data).
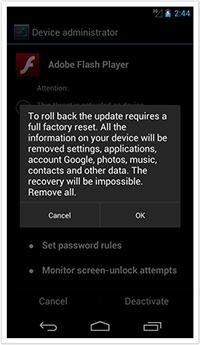
To remove these malicious programs, the user needs to revoke administrator privileges granted to the malware. However, these Trojans will try to prevent the user from completing the procedure by informing them that all the data stored on the device will be permanently lost.
Vulnerabilities for Android
According to statistics, every fifth program for Android contains a vulnerability (or, in other words, a "loophole") that lets cybercriminals successfully introduce Trojans onto mobile devices and manipulate them into doing whatever actions they need them to.
Dr.Web Security Auditor for Android diagnoses and analyses a mobile device’s security and offers solutions to address security problems and vulnerabilities.