Virus library
An analysis of the technologies used by cybercriminals allows us to draw conclusions about the virus industry’s possible vectors of development and more effectively confront future threats. You, too, can learn what actions various malicious programs take in infected systems and how to withstand them.
Android.Subscription in virus library:
Trojan applications for Android that subscribe users to paid mobile services. They are distributed as different legitimate software, like photo and video editors, multimedia apps, various system tools, launchers, navigation apps, and so on. Many of these apps are phony and lack any functionality. Others have minimal capabilities or can work completely different from what users would expect. Some of them can hide inside copies of initially harmless apps that malicious actors have modified.
When launched, trojans from the Android.Subscription family use a WebView system component. They will load affiliate services websites that activate paid subscriptions using Wap Click technology. These pages may contain specialized buttons with various content, banners, and other interactive elements. They may also have fields and forms to provide a mobile phone number. When the user taps these elements or provides a phone number, an attempt is made to automatically activate a paid service.
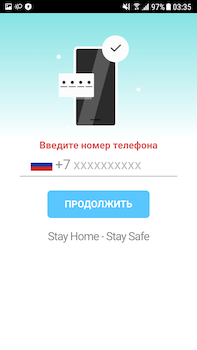
Below is an example of an affiliate service web page loaded by Android.Subscription trojans. This page is asking a potential victim for their mobile phone number.
Vulnerabilities for Android
According to statistics, every fifth program for Android contains a vulnerability (or, in other words, a "loophole") that lets cybercriminals successfully introduce Trojans onto mobile devices and manipulate them into doing whatever actions they need them to.
Dr.Web Security Auditor for Android diagnoses and analyses a mobile device’s security and offers solutions to address security problems and vulnerabilities.