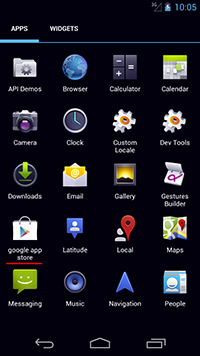
A banking Trojan that steals authentication information used by the clients of some South Korean financial organizations. It is distributed under the guise of a Google Play application.
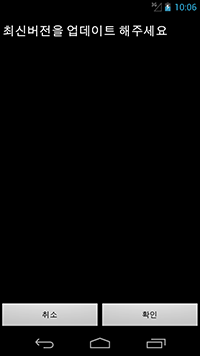
Once launched, Android.BankBot.29.origin attempts to acquire administrator privileges, while hiding the appropriate system prompt behind its own dialog box that asks the victim to install an allegedly new version of the program. By giving consent, the user allows the Trojan to acquire administrator privileges without knowing it.
Android.BankBot.29.origin steals authentication information from the following online banking applications used by South Korean financial organizations:
- nh.smart,
- com.shinhan.sbanking,
- com.epost.psf.sdsi,
- com.wooribank.pib.smart,
- com.hanabank.ebk.channel.android.hananbank,
- com.kbstar.kbbank,
- com.kftc.dgbsmb,
- com.keb.android.mbank,
- com.smg.spbs,
- com.cu.sb,
- com.kftc.citismb,
- com.ibk.neobanking,
- com.areo.bs,
- com.knb.psb,
- com.kftc.jbsmb,
- com.kftc.jejusmb,
- com.kftc.kjbsmb.
Once one of these programs is launched, the malware replaces its interface with a fake one that prompts the user to enter all the confidential information necessary to control their bank account. The divulged data is forwarded to cybercriminals.
Under the pretext of subscribing the user to a banking service, Android.BankBot.29.origin attempts to install the malicious program Android.Banker.32.origin that is stored in the Trojan’s body.