Virus library
An analysis of the technologies used by cybercriminals allows us to draw conclusions about the virus industry’s possible vectors of development and more effectively confront future threats. You, too, can learn what actions various malicious programs take in infected systems and how to withstand them.
Android.Pincer in virus library:
Android.Pincer is a family of malicious software running on Android mobile devices. The main purpose of this malware is to intercept incoming text messages and forward them to the violator.
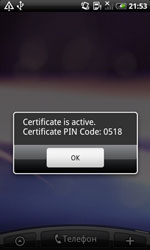
If started by careless users, the Android.Pincer Trojans display a message about supposedly successful installation of a security certificate to the mobile device.
These malicious programs can be loaded with the operating system bootup as a background service. For this, the malware registers an appropriate system service.
After loading, Android.Pincer Trojans are connecting to a remote server, which address can differ for each version of the malware (for example, http://89.144.xx.xxx/gate/gate.php, https://img-xxxxx.com/android_panel/gate.php), and uploading the following information about the mobile device to the server:
- device model;
- device serial number;
- IMEI number;
- telecom operator name;
- mobile phone number;
- default system language;
- operation system version;
- root-access availability details.
Then these malicious programs are waiting for further instructions via SMS control messages of the “command: [command name]" structure. Cybercriminals may provide one of the following directives:
- start_sms_forwarding [phone number] – start intercepting messages from the specified phone number;
- stop_sms_forwarding – stop intercepting messages;
- send_sms [phone number and text] – send an SMS with the specified parameters;
- simple_execute_ussd – perform a USSD-request;
- stop_program – stop working;
- show_message – display a message on the mobile device screen;
- set_urls – change address of the C&C server;
- ping – send an SMS with text “pong” to the phone number specified earlier;
- set_sms_number – change the phone number to which the “pong” text is sent.
Android.Pincer Trojans send contents of intercepted text messages to the C&C server while also providing subscriber’s name and phone number for each SMS.
Vulnerabilities for Android
According to statistics, every fifth program for Android contains a vulnerability (or, in other words, a "loophole") that lets cybercriminals successfully introduce Trojans onto mobile devices and manipulate them into doing whatever actions they need them to.
Dr.Web Security Auditor for Android diagnoses and analyses a mobile device’s security and offers solutions to address security problems and vulnerabilities.